QuillAudits First Version of Claude Skills Helps Identify Bugs in Smart Contracts
QuillAudits V1 Claude Skills help detect bugs and vulnerabilities in smart contracts, enabling faster, AI-powered security audits for developers.
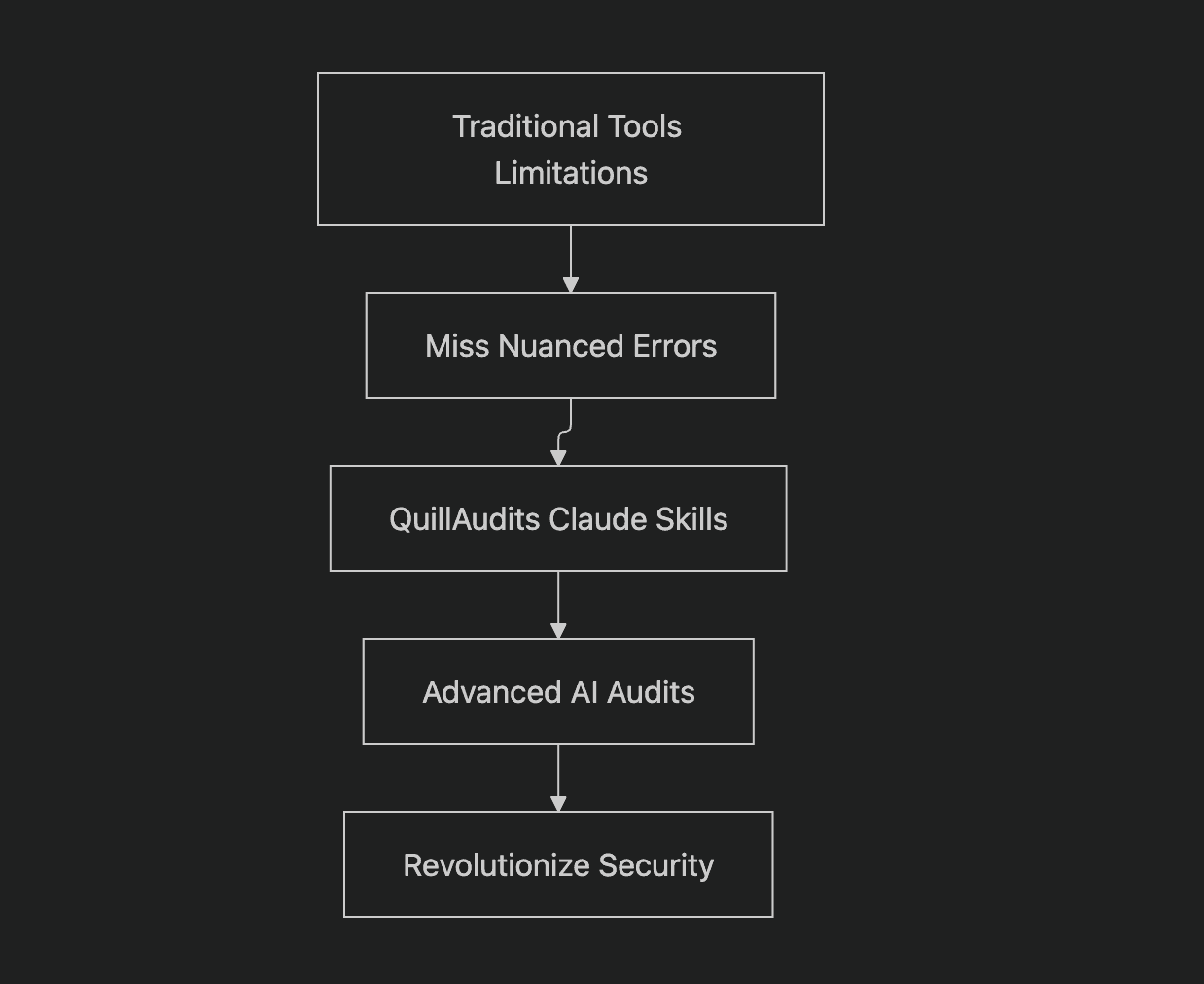
In blockchain security, where DeFi protocols safeguard billions in assets, a single vulnerability can trigger catastrophic losses. Traditional static analysis tools, while effective at detecting known patterns, often miss subtle logic flaws, state inconsistencies, and complex attack paths that require deeper semantic reasoning.
To bridge this gap, QuillAudits has released open-source AI agent skills under the QuillShield banner, available on this GitHub repository. Designed for seamless Claude integration, these skills enable advanced AI-assisted smart contract audits using the same methodology embedded in QuillAudits proprietary QuillShield engine.
By combining behavioral decomposition, adversarial simulation, invariant inference, and probabilistic risk scoring, the system shifts auditing from pattern matching to intent-based analysis. Rather than replacing researchers, it augments them with structured, AI-driven threat modeling.
In this blog, we explore the architecture, technical foundations, and practical applications of QuillAudits Claude Skills and how they are reshaping modern smart contract security workflow
The QuillShield Methodology: A Semantic Approach to AI-Enhanced Auditing
At the core of QuillAudits Claude Skills is the Semantic State Protocol, a research-driven framework that changes how AI analyzes smart contracts. Instead of relying on predefined patterns, the protocol treats the contract’s code as its own specification. This allows AI to extract behavioral intent, identify security guards (e.g., require statements and modifiers), and infer state invariants without external assumptions, enabling deeper, intent-based vulnerability detection.
The methodology operates in structured phases. It begins with behavioral decomposition, mapping core intents such as transfers and access control. Next, multi-dimensional threat modeling evaluates economic incentives, permission boundaries, and state integrity risks. Adversarial simulation then generates proof-of-concept exploits to validate hypotheses. Finally, Bayesian confidence scoring assigns probabilistic risk levels using historical exploit priors.
These capabilities transform Claude into a reasoning-driven virtual auditor. The same framework powers QuillShield’s proprietary AI engine, while the open-source Claude plugins (MIT licensed) allow researchers to customize, extend, and integrate the skills seamlessly into their workflows via marketplace.json or SKILL.md references in tools like Cursor.

Quick Start for Integrating Claude Skills
Getting started with QuillAudits’Claude Skills is simple and modular. Claude users can install the repository as a plugin, configured through .claude-plugin/marketplace.json. After setup, researchers can enable skills based on audit scope, use Behavioral State Analysis for full-spectrum reviews, or activate targeted plugins like Reentrancy Pattern Analysis for focused checks.
Integration with Cursor is equally flexible. Researchers can reference a skill directly within prompts (e.g., via the relevant SKILL.md path) or copy the skills directory into their local Cursor environment for direct access.
The key advantage is selective activation, each plugin is purpose-built for a specific threat domain. This modular architecture allows precise, context-aware AI assistance, whether auditing a simple ERC-20 token or a complex, multi-protocol DeFi system, without unnecessary overhead.

In-Depth Overview of QuillAudits Claude Skills
QuillAudits has developed 10 specialized Claude Skills, each organized within its own plugin directory. Every skill includes a plugin.json for configuration, a README.md for usage guidance, a core SKILL.md containing AI instructions, and a references folder with deeper technical documentation.
These skills are designed to detect vulnerabilities that traditional static tools often miss, including categories outlined in the OWASP Smart Contract Top 10 (2025).
In the sections below, we break down each skill, covering its detection logic, practical use cases, and how it integrates with the broader QuillShield AI auditing engine.
1. Behavioral State Analysis (BSA)
Plugin Path: plugins/behavioral-state-analysis/
Behavioral State Analysis (BSA) is the most comprehensive Claude Skill, delivering full-spectrum smart contract audits. It begins with behavioral intent extraction, mapping core functions and their objectives. The system then applies multi-dimensional threat modeling across economic incentives, access controls, and state integrity risks.
Next, adversarial simulation generates proof-of-concept exploit paths to validate detected weaknesses. Finally, Bayesian confidence scoring assigns probabilistic severity levels based on accumulated evidence and historical exploit patterns.
Supporting documentation includes threat-engines.md (threat modeling logic) and confidence-scoring.md (risk quantification framework).
Within QuillShield’s AI engine, BSA powers end-to-end audits. For researchers, it serves as the ideal starting point for reviewing DeFi protocols, modeling attacker behavior, or generating structured exploit demonstrations.

2. Semantic Guard Analysis
Plugin Path: plugins/semantic-guard-analysis/
Semantic Guard Analysis targets logic vulnerabilities by detecting inconsistencies in security guard usage. It builds a usage graph of require statements and modifiers, flagging functions that bypass checks enforced elsewhere (Consistency Principle), such as missing pause or access controls.
The detection-algorithm.md details the graph-based logic, while case-studies.md covers real-world incidents involving overlooked guards.
Integrated into QuillShield for automated logic validation, this skill helps researchers uncover subtle bugs that traditional pattern-matching tools often miss.

3. State Invariant Detection
Plugin Path: plugins/state-invariant-detection/
State Invariant Detection automatically infers mathematical relationships between state variables, such as supply sums, conservation rules, ratios (e.g., collateral-to-debt), monotonic counters, and synchronized updates. It then audits functions for invariant violations, identifying accounting desyncs and logic breaks.
invariant-types.md categorizes supported relationships, while case-studies.md examines real DeFi failures.
Within QuillShield, this skill strengthens tokenomics validation. For researchers, it’s essential for detecting supply mismatches, balance inconsistencies, and silent accounting errors.

4. Reentrancy Pattern Analysis
Plugin Path: plugins/reentrancy-pattern-analysis/
Reentrancy Pattern Analysis detects multiple reentrancy variants, including classic (withdraw-then-reenter), cross-function, cross-contract, read-only, and callback-based (ERC-777/ERC-1155). It builds call graphs, verifies Checks-Effects-Interactions (CEI) compliance, and traces state changes around external calls.
reentrancy-variants.md defines the attack taxonomy, and case-studies.md reviews major exploits.
In QuillShield, this skill is central to external call security. Researchers apply it when auditing multi-contract architectures and complex token interactions.

Audit Smarter with QuillAudits!
Audit Smarter with QuillAudits!
From behavioral state analysis to probabilistic risk scoring, we deliver AI-augmented audits designed for modern DeFi and complex smart contract systems.
5. Oracle & Flash Loan Analysis
Plugin Path: plugins/oracle-flashloan-analysis/
Oracle & Flash Loan Analysis targets price manipulation and atomic liquidity attacks. It classifies oracle models (e.g., decentralized feeds, TWAP, spot pricing) and detects staleness, circular dependencies, and flash loan exploit paths (borrow–manipulate–repay in one transaction).
oracle-types.md outlines oracle trust assumptions, while flash-loan-vectors.md documents common attack patterns.
Within QuillShield, this skill secures price-dependent logic. Researchers use it for lending protocols, AMMs, and any system reliant on external price feeds.

6. Proxy & Upgrade Safety
Plugin Path: plugins/proxy-upgrade-safety/
Proxy & Upgrade Safety analyzes upgradeable contract patterns, including Transparent, UUPS, Beacon, Diamond (EIP-2535), and Minimal proxies. It detects storage layout collisions, uninitialized implementations, function selector clashes, and unsafe upgrade paths.
proxy-patterns.md documents supported architectures, while storage-collision-detection.md details slot analysis logic.
In QuillShield, this skill strengthens delegatecall and upgrade reviews. Researchers rely on it when auditing proxy-based systems and implementation migrations.

7. Input & Arithmetic Safety
Plugin Path: plugins/input-arithmetic-safety/
Input & Arithmetic Safety validates function inputs and numerical operations, addressing precision loss, rounding exploits, ERC-4626 inflation vectors, unsafe type casting, and unchecked arithmetic risks in Solidity 0.8+.
precision-patterns.md covers calculation edge cases, while validation-checklist.md defines required input checks.
In QuillShield, this skill strengthens public function validation. Researchers apply it to fee logic, pricing models, and vault accounting mechanisms.

8. External Call Safety
Plugin Path: plugins/external-call-safety/
External Call Safety analyzes risks in third-party interactions, including unchecked return values, fee-on-transfer and rebasing tokens, missing ERC-20 return patterns, unsafe approvals, callbacks, and push-vs-pull payment flows.
weird-erc20.md documents non-standard token behaviors, while call-safety-patterns.md outlines secure interaction practices.
Within QuillShield, this skill strengthens token integration reviews. Researchers use it to secure payment flows, token transfers, and external contract dependencies.

9. Signature & Replay Analysis
Plugin Path: plugins/signature-replay-analysis/
Signature & Replay Analysis detects replay vulnerabilities, including same-chain, cross-chain/contract, nonce-skipping, and expired signature attacks. It validates EIP-712 domain separation, ecrecover usage, ECDSA flows, and permit/permit2 implementations.
replay-taxonomy.md defines replay categories, while eip712-checklist.md provides verification checks.
In QuillShield, this skill secures off-chain signature validation. Researchers use it to audit meta-transactions, permit flows, and signature-based authorization logic.

10. DoS & Griefing Analysis
Plugin Path: plugins/dos-griefing-analysis/
DoS & Griefing Analysis identifies denial-of-service vectors, including unbounded loops, gas exhaustion, external call failures, 63/64 gas griefing, storage bloat, timestamp manipulation, and forced Ether transfers via self-destruct.
dos-patterns.md catalogs attack patterns, while gas-griefing-vectors.md outlines common gas-based exploits.
Within QuillShield, this skill strengthens batch execution and system resilience. Researchers apply it to reward mechanisms, distribution logic, and high-iteration contract flows.

QuillShield's Modular Architecture
The project architecture is modular and extensible. A root marketplace.json configures Claude integration, while individual plugins/ directories contain per-skill files and documentation.
This structure allows researchers to selectively combine skills based on audit scope—mirroring how QuillShield orchestrates multiple modules for automated, layered security analysis.

This mindmap provides a high-level view of the architecture.
Interrelations Among Skills: A Layered Framework
The skills are interconnected, with Behavioral State Analysis (BSA) acting as the central hub. It integrates foundational layers (guard consistency and invariant checks) with extended modules (specialized vulnerability analyses).
This layered design enables compounded detection, where insights from one skill reinforce and inform others, producing deeper, cross-domain security validation.

This graph shows the basic layering.
Alignment with Industry Standards: OWASP Coverage
QuillAudits Claude Skills deliver comprehensive coverage of the OWASP Smart Contract Top 10 (2025), enabling researchers to systematically address the most critical and recurring smart contract risk categories.
| OWASP Category | QuillShield Skill | Coverage |
|---|---|---|
| SC01: Access Control | Semantic Guard Analysis | Full |
| SC02: Oracle Manipulation | Oracle & Flash Loan Analysis | Full |
| SC03: Logic Errors | BSA + State Invariant Detection | Full |
| SC04: Input Validation | Input & Arithmetic Safety | Full |
| SC05: Reentrancy | Reentrancy Pattern Analysis | Full |
| SC06: Unchecked External Calls | External Call Safety | Full |
| SC07: Flash Loan Attacks | Oracle & Flash Loan Analysis | Full |
| SC08: Integer Overflow | Input & Arithmetic Safety | Full |
| SC09: Insecure Randomness | BSA Threat Engines | Partial |
| SC10: DoS Attacks | DoS & Griefing Analysis | Full |
Beyond this, skills extend to niche areas:
| Category | QuillShield Skill |
|---|---|
| Proxy/Upgrade Vulnerabilities | Proxy & Upgrade Safety |
| Signature Replay Attacks | Signature & Replay Analysis |
| Token Integration (Weird ERC20) | External Call Safety |
| MEV/Frontrunning | Oracle & Flash Loan Analysis |

Risk Prioritization: The Multi-Layer Severity Matrix
To support structured risk assessment, QuillAudits incorporates a severity matrix that aggregates findings across layers, enabling consistent and evidence-based vulnerability prioritization.
| Layer 1 (Guard) | Layer 2 (Invariant) | Layer 3+ (Extended) | Combined Severity |
|---|---|---|---|
| Missing Guard | Breaks Invariant | Additional Vuln | CRITICAL |
| Missing Guard | Breaks Invariant | No Additional | CRITICAL |
| Missing Guard | No Break | Additional Vuln | HIGH |
| Missing Guard | No Break | No Additional | HIGH |
| No Issue | Breaks Invariant | Additional Vuln | HIGH |
| No Issue | Breaks Invariant | No Additional | HIGH |
| No Issue | No Break | Additional Vuln | MEDIUM-HIGH |
| No Issue | No Break | No Additional | LOW/INFO |

This flowchart depicts severity levels.
Research Foundations and Community Engagement
These skills are built on the QuillShield Semantic State Protocol, reinforced by OWASP 2025 guidance, security methodologies from hybrid AI-symbolic research, and lessons from major exploits such as The DAO, Euler, Mango Markets, Curve, and Nomad Bridge.
Core references include newApproach.md (BSA framework), semantic_state_protocol.md (guard analysis), and semantic_state_to_state_protocol.md (invariant modeling).
The project is open to contributions via CONTRIBUTING.md, encouraging collaborative advancement in AI-driven smart contract security.

The Future of AI in Smart Contract Security
QuillAudits Claude Skills, which power the QuillShield AI engine, mark a significant shift in smart contract security. By automating semantic analysis, adversarial simulation, and probabilistic risk scoring, they accelerate audits while improving analytical depth.
As blockchain systems grow more complex, AI-assisted methodologies challenge purely manual approaches and redefine audit efficiency. For researchers, integrating these skills is a strategic step toward staying competitive in the evolving security landscape.

Conclusion
QuillAudits Claude Skills represent a shift from reactive pattern detection to proactive, intent-driven security analysis. By combining semantic reasoning, adversarial simulation, and probabilistic scoring within a modular, open-source framework, QuillShield empowers researchers to audit with greater depth, structure, and confidence. Rather than replacing human expertise, it amplifies it, transforming Claude into a reasoning-driven audit companion. As DeFi systems grow increasingly complex, AI-augmented workflows like these will define the next standard in smart contract security, i.e., faster, smarter and grounded in measurable risk intelligence.
Contents




