RWA Security Risks and Best Practices: Securing Tokenized Assets End-to-End
Explore RWA security risks and best practices to protect tokenized assets. Learn how to secure real-world asset protocols end-to-end.

Real-world asset tokenization is the process of issuing blockchain tokens that represent ownership, claims, or economic exposure to off-chain assets such as U.S. Treasuries, private credit, real estate, commodities, fund shares, and more. The market is no longer experimental, it's an institutional-scale infrastructure.
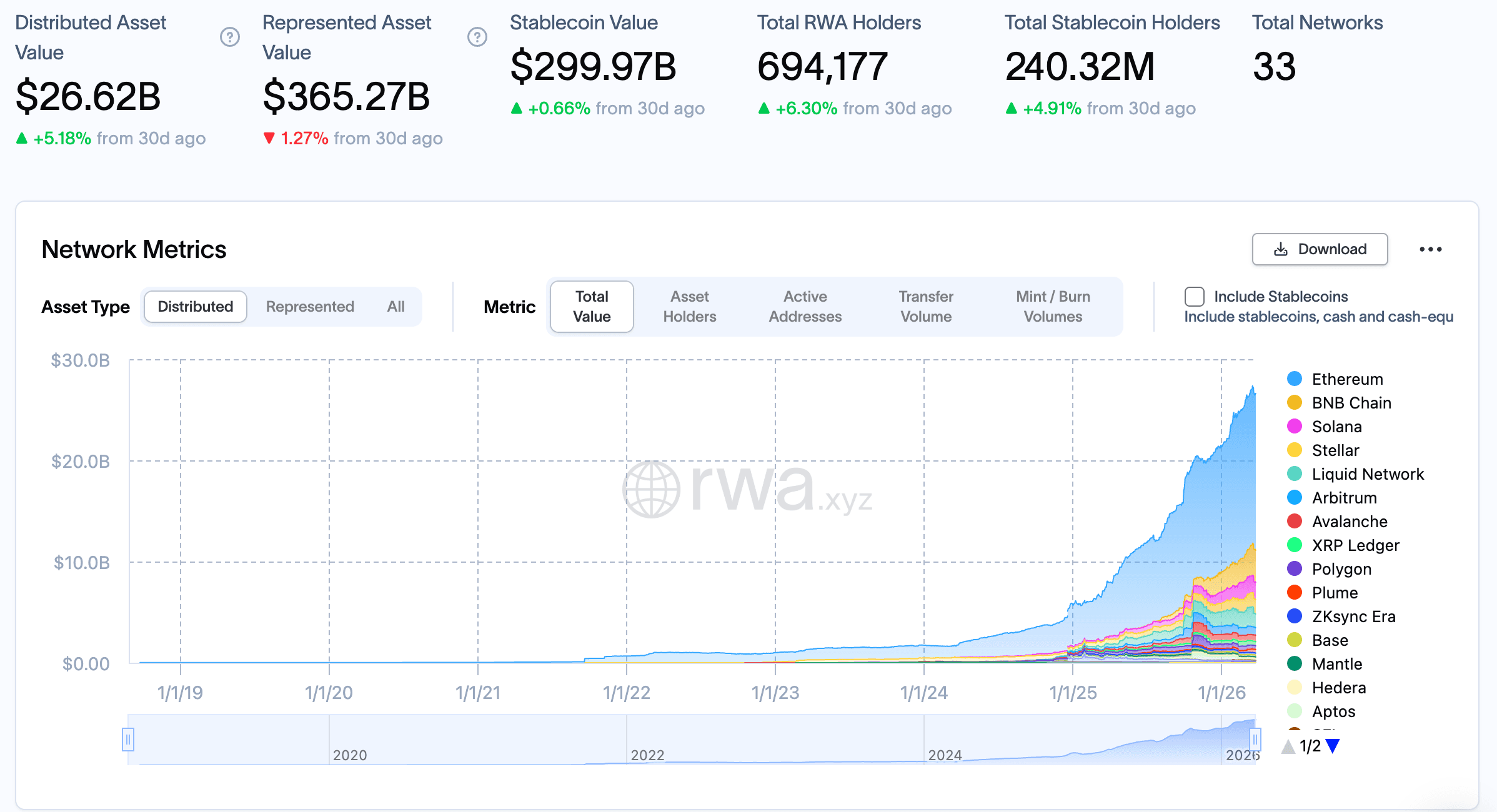
As of March 2026, according to rwa.xyz, distributed asset value has reached $26.69B (up 5.33% in 30 days) with a represented asset value of $360.52B. The ecosystem now spans 33 networks, from Ethereum and Solana to Stellar, Arbitrum, BnB and Base, with nearly 700,000 RWA holders and growing. The stablecoin market alone, which functions as a settlement and liquidity rail for tokenized assets, sits above $300B.
Major institutional asset managers, tokenization platforms, and DeFi native protocols have moved from pilots to live, institutional-grade products. For a comprehensive deep-dive into how these protocols are architecturally designed, how they handle custody and compliance, and which token standards they use, the QuillAudits RWA Development Handbook is an essential reference, covering ecosystem landscape, regulatory mapping, developer foundations, and both EVM and non-EVM token standards from ERC-3643 to Solana Token-2022.
But the security model for RWAs is fundamentally different from pure DeFi. In a standard DeFi protocol, the smart contract is the product. If the contract is sound, the system works. With RWAs, the on-chain token is a claim on something that exists off-chain, a bond in a custodian's vault, a loan on a borrower's balance sheet, a deed in a land registry. This means the attack surface extends well beyond what traditional DeFi audit frameworks were designed to cover.
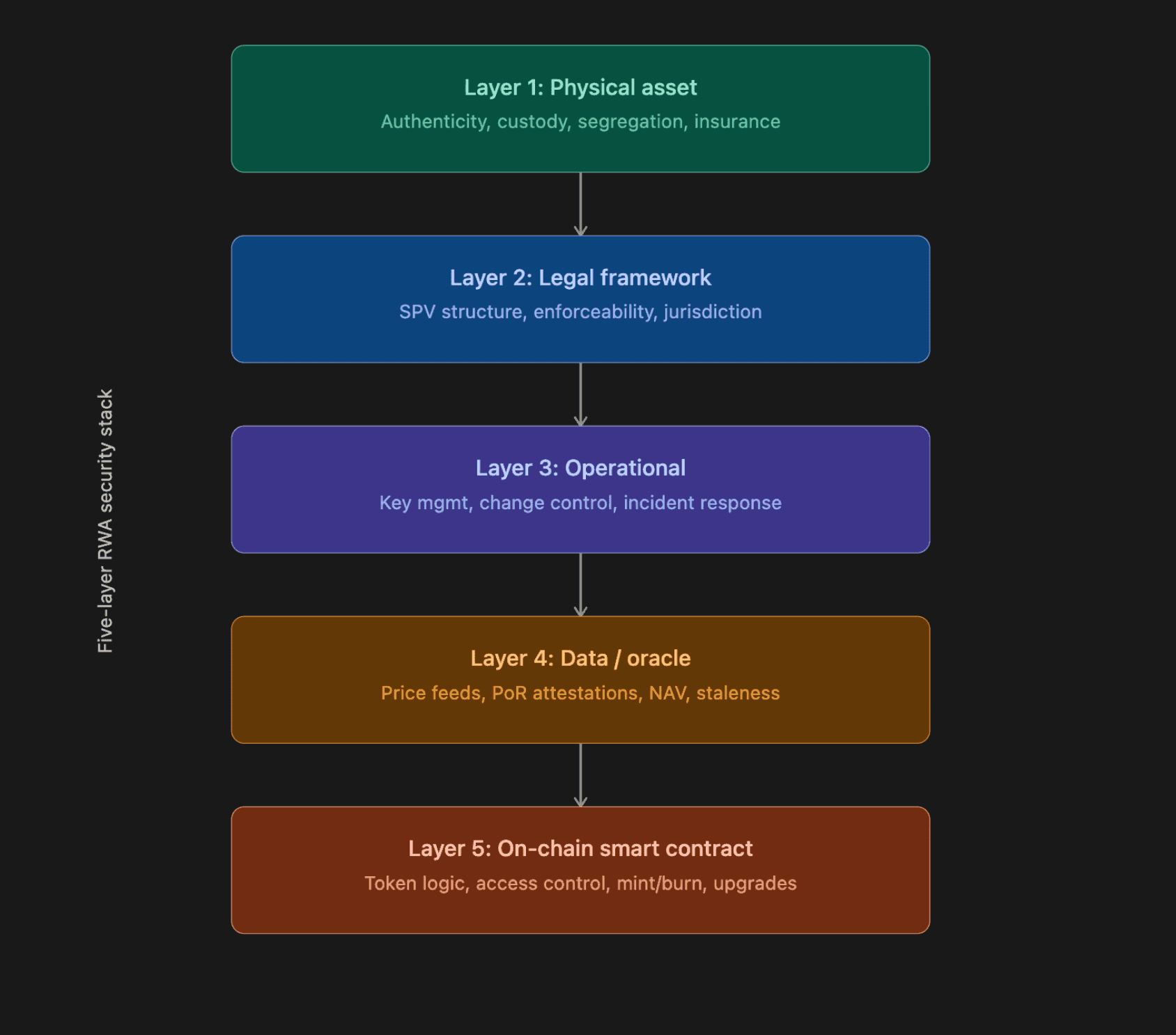
The industry has begun to formalize this insight through a five-layer security stack model that covers, the physical asset layer, the legal framework layer, the operational layer, the data/oracle layer, and the on-chain smart contract layer. Each layer can present a single point of vulnerability. Off-chain processes introduce unique risks because they involve human actors, are subject to legal interpretation, and follow operational workflows that smart contract auditors rarely examine.
Audits of leading RWA protocols, including tokenized Treasury products integrated with institutional fund managers, have reinforced this perspective that RWA protocols require auditors who understand the intersection of blockchain security, traditional finance, and regulatory compliance, not just Solidity expertise.
The data backs this up. Industry security research shows that direct losses from RWA specific exploits reached $14.6 million in H1 2025 alone, more than double the $6 million lost in all of 2024, and approaching the $17.9 million lost in 2023. More importantly, the nature of the attacks has shifted. In 2023 and 2024, the primary threats came from off-chain credit defaults, borrowers failing to perform. By 2025, losses were driven almost entirely by on-chain and operational failures, oracle misconfigurations, and access control logic bugs, and some are from compromised private keys. This signals a clear transformation in the RWA threat landscape.
Core RWA Security Risks
In this section, we break down the core security risks unique to Real World Asset (RWA) protocols. From asset - token mismatches to oracle failures and custody assumptions, each risk highlights how combining on-chain logic with off-chain dependencies introduces new attack surfaces. Understanding these risks is essential to designing secure, resilient tokenization systems.
Asset–Token Mismatch
The most basic RWA risk is deceptively simple: does the token supply reliably map to the underlying asset? If a protocol claims 1,000 tokens represent $1,000,000 in Treasury bills, what happens when 1,200 tokens exist but only $1,000,000 in reserves back them?
This mismatch can emerge from bugs in mint/burn logic, from off-chain reserve movements that aren't reflected on-chain, or from fraudulent proof-of-reserve attestations that report collateral that doesn't exist. Security researchers have specifically flagged fraudulent PoR attestations as a key hybrid threat, on-chain verification is only as trustworthy as the attestor providing the data. The on-chain contract has no way to verify that the custodian actually holds the asset independently.
Mint and Burn Abuse
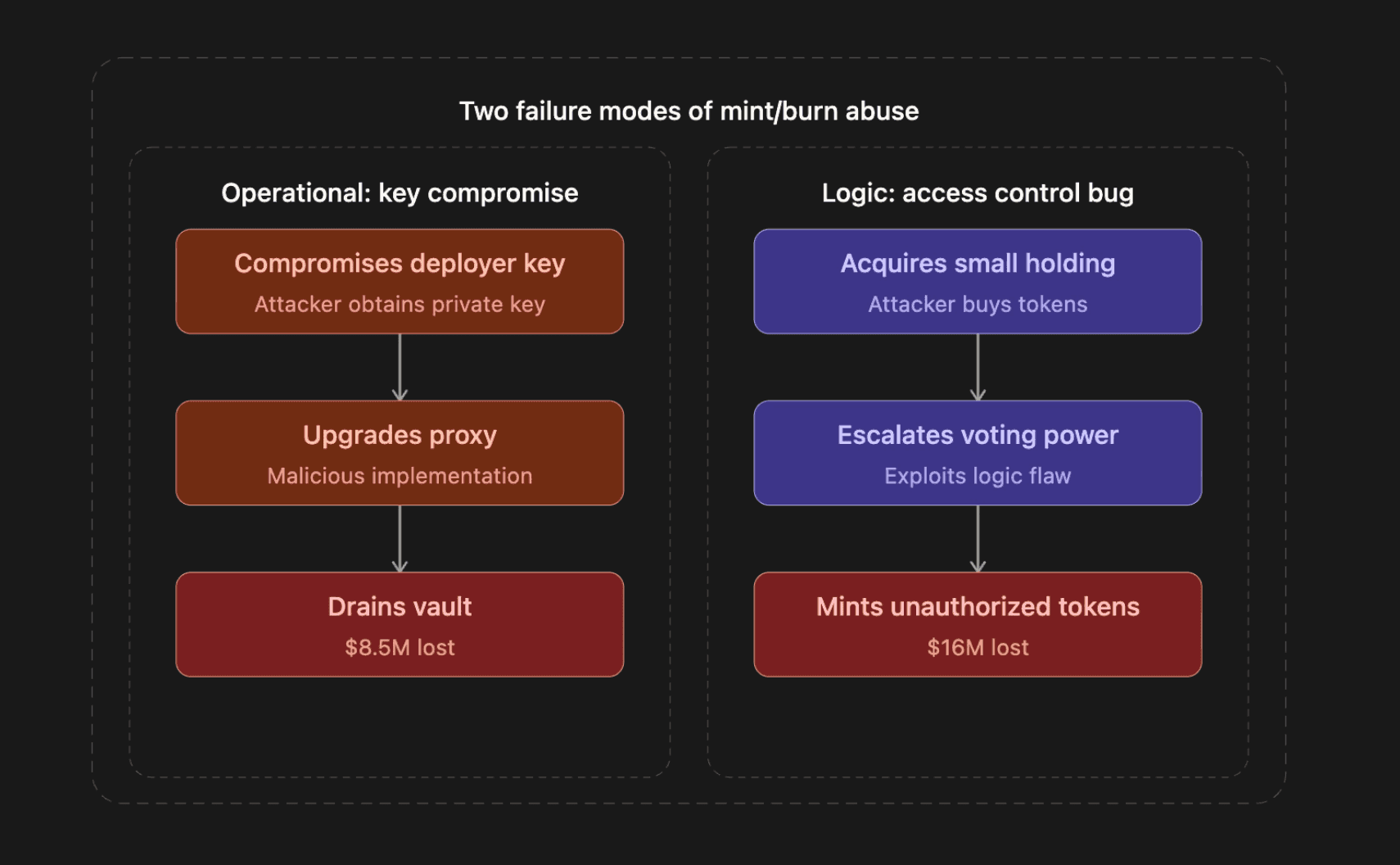
Unauthorized issuance or redemption is the fastest path to catastrophic loss in an RWA protocol. Two real-world incidents illustrate the two distinct failure modes:
$8.5M RWA Restaking Exploit (March 2025) Operational key compromise: An RWA restaking protocol lost $8.5 million when an attacker compromised the deployer wallet's private key. Post-mortem analysis revealed the attacker used the stolen key to call upgradeToAndCall on a proxy contract, replacing the legitimate implementation with a malicious one that granted full control over the vault. Within minutes, $8.4 million in stablecoins was drained, swapped to DAI, and converted to approximately 4,223 ETH. The root cause: a single private key controlled upgrade privileges, no multisig, no timelock, no secondary approval. Security researchers classified this as a classic operational security failure.
$16M RWA Governance Exploit (March 2024) Access control logic bug: An RWA liquidity firm suffered a smart contract exploit when an attacker exploited a flaw in the voting power privilege access control within a MakerDAO-based smart contract. By acquiring a small number of governance tokens, the attacker elevated their voting power, gained the ability to execute arbitrary actions within the DAO contract, and minted 1 billion unauthorized tokens. Security analysts classified it as a permission access logic vulnerability. The attack didn't require sophisticated techniques, just a flawed governance threshold that allowed privilege escalation with minimal token holdings.
Privilege Risk
Admin keys, upgradeability, and emergency controls are necessary in RWA protocols, compliance requirements, regulatory mandates, and the need to respond to off-chain events all demand some level of centralized control. But every privileged function is a potential single point of failure.
This creates a unique tension in RWA security. Audits of major RWA tokenization protocols have revealed that some include the ability for admins to seize user assets, a feature that exists to comply with regulatory requirements and court orders, not a bug. Understanding which centralization is necessary versus which creates unacceptable risk is a judgment call that requires traditional finance knowledge, not just smart contract expertise.
The March 2025 restaking exploit is a textbook case of the downside. Security professionals noted that the attack could have been prevented by implementing multisig contract upgrades to prevent single-point failures, adding timelocks on upgrades to allow monitoring, and placing real-time alerts for admin role changes. Admin key compromises remain a major risk across the DeFi ecosystem.

Oracle and Pricing Risk
Oracle misconfiguration is the single most commonly exploited vulnerability in RWA adjacent protocols. Two incidents demonstrate the cascading damage a mispriced feed can cause:
$1.78M Oracle Misconfiguration (February 2026): A DeFi lending protocol lost $1.78 million when a governance proposal misconfigured an oracle wrapper on its Base deployment. According to the protocol's own post-mortem, the oracle used only the raw cbETH/ETH exchange rate instead of multiplying it by the ETH/USD price, causing cbETH to be reported at approximately $1.12 instead of its market value near $2,200. Liquidation bots immediately exploited the mispricing, over 1,096 cbETH was liquidated, and the protocol was left with $1.78 million in bad debt. The monitoring system detected the error within minutes, but the governance timelock required a five-day voting period to correct the oracle, during which liquidations continued. The same protocol had suffered three oracle-related incidents in the past six months, accumulating over $7 million in total bad debt.
$5.8M Oracle Manipulation (April 2025): A Solana-based lending protocol was drained of $5.8 million (5.7M USDC and 1,200 SOL) when an attacker manipulated the pricing of a principal token used as collateral. The attacker identified a low-liquidity trading pair feeding the protocol's oracle, injected minimal capital to create artificial price movement, and used the inflated price to take out undercollateralized loans. The vulnerability had been flagged in a prior audit, but the fix was not implemented properly before launch. The protocol had been live for only two weeks. The attacker later accepted a 10% whitehat bounty and returned the funds in full.
For RWA protocols specifically, oracle risk extends beyond standard price feeds. NAV calculations for tokenized fund shares, proof-of-reserve attestations for backed stablecoins, and interest-rate feeds for private credit instruments all introduce oracle-like dependencies. In some tokenized Treasury products, the USD price is set every day by an off-chain oracle controlled by the protocol itself, a design that works for stable NAV products but creates a fundamentally different trust model than decentralized oracle feeds.
Here is a simplified example of what a price-feed sanity check should look like in Solidity, the kind of guard that would have caught the February 2026 oracle misconfiguration:
1// Oracle price sanity check — prevent catastrophic mispricing
2function getValidatedPrice(
3 AggregatorV3Interface feed,
4 uint256 maxStaleness,
5 uint256 minPrice,
6 uint256 maxPrice
7) internal view returns (uint256) {
8 (
9 uint80 roundId,
10 int256 answer,
11 ,
12 uint256 updatedAt,
13 uint80 answeredInRound
14 ) = feed.latestRoundData();
15
16 // Check for stale data
17 require(
18 block.timestamp - updatedAt <= maxStaleness,
19 "Oracle: stale price"
20 );
21
22 // Check round completeness
23 require(answeredInRound >= roundId, "Oracle: incomplete round");
24
25 // Check price is positive
26 require(answer > 0, "Oracle: non-positive price");
27
28 uint256 price = uint256(answer);
29
30 // Circuit breaker: reject prices outside expected bounds
31 require(
32 price >= minPrice && price <= maxPrice,
33 "Oracle: price outside circuit breaker bounds"
34 );
35
36 return price;
37}Custody and SPV Trust Assumptions
The custodian holds the real asset. If the custodian is compromised, insolvent, or simply uncooperative, the on-chain token becomes a claim on nothing. Key compromise, weak wallet policies, unclear custody models, and the lack of segregation between protocol assets and custodian operating funds are all live risks.
Most large RWA programs use a Special Purpose Vehicle (SPV) or custodian holding legal title off-chain, with the token representing a beneficial interest in that vehicle. As noted in a detailed analysis of RWA legal frameworks, courts examine contractual documentation, corporate structures, and whether the ledger entry is recognized by applicable law as evidencing title. Without statutory recognition, tokens often function as evidence of beneficial ownership rather than the sole legal title.
The on-chain contract cannot verify the SPV's solvency, the custodian's competence, or the legal enforceability of the claim. These are residual risks that auditors must flag explicitly. The five-layer security model explicitly positions custodial and counterparty failures as a distinct risk category alongside oracle manipulation and smart contract bugs, recognizing that no amount of on-chain verification can eliminate off-chain counterparty risk.
Industry security leaderboards reflect this: the highest-rated RWA protocols are those backed by major institutional asset managers, and they achieve their security posture primarily through institutional grade compliance, custody, and transparency, strengths that derive from their TradFi heritage, not from their smart contract architecture alone.
Compliance and Transfer Restrictions Risk
RWA tokens almost always embed compliance logic directly in the token contract: allowlists that restrict transfers to KYC-verified addresses, blocklists that freeze sanctioned wallets, jurisdiction checks that enforce investor eligibility. This compliance-as-code layer creates a new exploit surface that DeFi native auditors are not familiar to evaluating.
As security auditors have noted, the ERC-3643 standard alone requires identity registries, compliance contracts, trusted issuer registries, and claim verification systems, each component creating additional attack surface. A broken allowlist can lock legitimate holders out of their positions. A bypassable restriction can allow unverified parties to acquire regulated securities. A poorly implemented blocklist can be circumvented by transferring through an intermediary contract.
Standards like ERC-3643 (Token for Regulated Exchanges), ERC-7518 (Dynamic Compliant Interop Security Token), and ERC-1400 (Security Token Standard) each encode compliance differently, with varying approaches to identity registries, transfer agents, and partition based restrictions. Choosing the wrong standard, or implementing it incorrectly, introduces compliance gaps that are both a security risk and a regulatory liability. The QuillAudits RWA Development Handbook provides detailed breakdowns of each standard, including non-EVM equivalents like Solana Token-2022 and Stellar's native issuance protocol, helping teams make informed architectural decisions before writing a single line of code.
Third-Party Dependency Risk
RWA protocols depend on a web of external parties, bridge protocols for cross-chain transfers, attestors for proof-of-reserve, custodians for asset safekeeping, KYC providers for identity verification, and transfer agents for corporate actions. Each dependency is a trust assumption and a potential failure point.
Bridge exploits remain one of the largest categories of DeFi loss. When an RWA token is bridged cross-chain, the security guarantee of the token is now bounded by the weakest link in the bridge's validation logic. RWA growth is concentrated in key blockchains and protocols, but multi-chain deployments on Base, Arbitrum, Solana, and Stellar are growing. This concentration creates systemic exposure, a significant breach on a key chain or bridge could have cascading effects across the entire RWA ecosystem.
Specialized RWA audit frameworks now include auditing APIs, oracles, custodial bridges, and IPFS data flows, validating data authenticity, uptime, and fallback mechanisms for each external dependency. This level of third-party dependency auditing is rare in standard DeFi engagements but essential for RWA protocols.
Operational Risk
Incident response gaps, monitoring blind spots, and weak change management are the unglamorous risks that cause the most damage in practice. The February 2026 oracle incident is instructive: monitoring systems detected the oracle discrepancy within minutes, but the governance timelock required a five-day voting period to correct the oracle, during which liquidations continued. The protocol's own safety mechanism prevented a rapid fix.
International regulatory bodies have highlighted that many fund administrators, custodians, and distributors remain unable to process tokenized transactions seamlessly within existing infrastructure. Insufficient operational training across legal, compliance, and middle office teams makes onboarding tokenized assets more complex than the technology alone would suggest.
Operational risk also includes the gap between off-chain approvals and on-chain actions. When a compliance officer approves a token issuance via email, and a developer executes the on-chain mint, there is no auditable on-chain record linking the approval to the action. If the developer mints more than was approved, or mints to the wrong address, the discrepancy may not be caught until a reconciliation process that runs days or weeks later.
Security Best Practices for RWA Protocol Development
In this section, we translate the previously discussed risks into actionable security practices. These best practices cover smart contract design, oracle resilience, custody architecture, and operational readiness, providing a practical checklist for building secure and compliant RWA systems end-to-end.
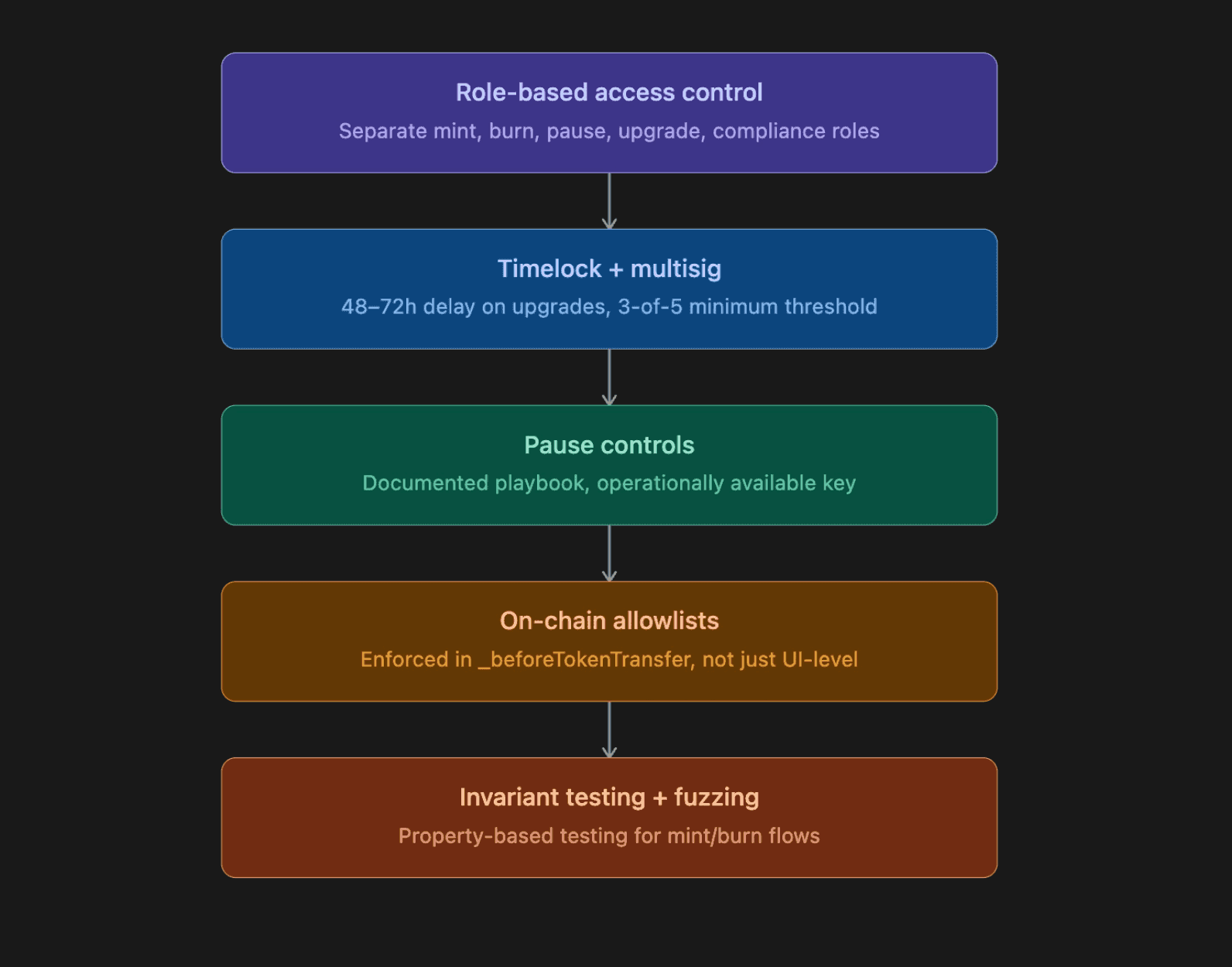
Smart Contracts
Use role-based access control with least privilege. Separate minting, burning, pausing, upgrading, and allowlist management into distinct roles. No single key should hold more than one critical privilege. OpenZeppelin's AccessControl with custom roles is the standard pattern:
1bytes32 public constant MINTER_ROLE = keccak256("MINTER_ROLE");
2bytes32 public constant PAUSER_ROLE = keccak256("PAUSER_ROLE");
3bytes32 public constant UPGRADER_ROLE = keccak256("UPGRADER_ROLE");
4bytes32 public constant COMPLIANCE_ROLE = keccak256("COMPLIANCE_ROLE");
5
6function mint(address to, uint256 amount)
7 external
8 onlyRole(MINTER_ROLE)
9{
10 require(amount <= mintCap, "Exceeds mint cap");
11 _mint(to, amount);
12 emit Minted(to, amount, msg.sender);
13}Put upgrades behind a timelock and multisig. Every contract upgrade should require a minimum delay (48–72 hours for non-emergency changes) and approval from a multi-sig or MPC wallet with a threshold of at least 3-of-5. The timelock gives the community and monitoring systems time to review proposed changes before they take effect. The March 2025 restaking exploit, where a single compromised key enabled an instant malicious upgrade, is the canonical example of what happens without these controls.
Add pause controls with clear, documented playbooks. A pause() function is useless if the team doesn't know when to call it, who has the authority, or what the escalation path is. Write the playbook. Make sure the pause key is held by an operationally available party, not a cold storage wallet that takes 48 hours to access.
Enforce allowlists on-chain if compliance requires it. Don't rely on front-end restrictions alone. If a token can only be held by accredited investors, the transfer restriction must be enforced at the contract level, in the _beforeTokenTransfer hook, not in a UI gate that a direct contract call bypasses.
Test invariants and include fuzzing for critical flows. Mint/burn invariants (total supply must equal sum of balances, total supply must not exceed collateral attestation) should be tested with property-based fuzzing tools like Foundry's fuzzer or Echidna. Published audits of major tokenized Treasury protocols have found issues including broken rate limiter invariants, where investor records could be created associated with the zero address, demonstrating that even well-resourced protocols have edge cases that only rigorous invariant testing catches.
Oracles and Data Integrity
Use multiple sources or a resilient design with circuit breakers. A single oracle feed is a single point of failure. Aggregate from multiple sources where possible, and implement circuit breakers that halt protocol operations when a price deviates beyond a configurable threshold. The February 2026 oracle misconfiguration, where an asset was mispriced by 99.95%, would have been caught by a circuit breaker that rejected extreme deviation. The April 2025 oracle manipulation, where a low-liquidity pair was exploited, would have been mitigated by volume weighted or TWAP based pricing that resists thin market manipulation.
Monitor staleness and deviation thresholds. Set explicit maximum staleness windows for every feed your protocol consumes. For volatile assets, 1 hour may be too long. For stable NAV feeds on money market funds, 24 hours may be acceptable. Monitor these thresholds actively, don't rely on on-chain checks alone.
Add a safe fallback strategy and document when it can trigger. When the primary oracle fails, what happens? A well-designed fallback might pause new borrows, prevent liquidations, or switch to a secondary feed with wider circuit-breaker bounds. Document the conditions under which each fallback activates, and test the fallback path with the same rigor as the primary path. Mature RWA audit methodologies now include real-time oracle simulation and failure injection stress-testing what happens when feeds go stale, return extreme values, or stop responding entirely.
Custody and Reserves
Define custody architecture clearly. Who holds the asset? Under what legal structure? What happens in the custodian's insolvency? Is the asset segregated from the custodian's operating assets? These questions should have documented with publicly available answers.
Use multisig or MPC for treasury and privileged roles. Every wallet that can mint tokens, upgrade contracts, or move treasury funds should be protected by a multi-sig (Safe or equivalent) or MPC wallet. Single-key wallets for privileged operations are an unacceptable risk at any scale. The March 2025 restaking exploit, where a single deployer key led to $8.5M in losses, is the clearest possible demonstration of this principle.
Maintain auditable proof of reserves or attestations. Proof-of-reserve systems should publish attestations on a regular cadence (daily or weekly, depending on the asset class) with enough detail to be independently verified. On-chain PoR feeds add a layer of automated verification, but they are only as trustworthy as the attestor providing the data. Fraudulent PoR attestations, where the attestor reports reserves that don't exist, have been identified as a key RWA threat vector. Circuit breakers and independent audits must catch attestations that misrepresent the actual reserves.
Operations
Ship monitoring for privileged actions, mint, burn, upgrades, and large transfers. Every privileged transaction should trigger an alert in a real-time monitoring system (tools like OpenZeppelin Defender, Forta, or Tenderly are widely used). Large transfers above a configurable threshold should be flagged for manual review. Upgrade transactions should trigger a high-severity alert regardless of whether they pass through a timelock.
Maintain an incident response plan and run tabletop drills. The plan should cover scenarios including: compromised admin key, oracle failure, custodian insolvency, regulatory freeze order, bridge exploit affecting bridged tokens, and proof-of-reserve attestation failure. Run tabletop exercises quarterly with the full team, engineering, compliance, legal, and operations. Enterprises need structured governance models covering stakeholder accountability, voting rights, and asset management rules, audits prevent problems, but operational measures ensure resilience facing hacks, mismanagement, or regulatory shocks.
Keep an audit trail for off-chain approvals that trigger on-chain actions. When a compliance officer approves a mint, that approval should be logged in an immutable system (even if it's just a signed message stored off-chain) with a reference to the on-chain transaction it authorizes. The audit trail should be reviewable by external auditors and regulators.
Key Focus Areas in RWA Security Audits
Based on published audit reports and post-mortem analyses across the RWA sector, the following areas consistently surface as critical focus points in security engagements:
Privileged flows and upgrade paths. Trace every path that can change token supply (mint, burn, rebase, fee collection) and confirm that each path has appropriate authorization and event emission. Verify that every onlyRole or onlyOwner function is protected by a multisig with a timelock. The March 2024 governance exploit, where a threshold flaw allowed privilege escalation with minimal token holdings, demonstrates why access control testing must go beyond checking that modifiers exist. Auditors must verify that the thresholds and logic behind privilege grants are sound.
Mint/burn and redemption logic. Audits of major tokenized Treasury protocols have found issues including rate limiter invariant breaks and edge cases in institutional fund redemption and contract integration. Best-in-class audit methodologies stress-test mint/burn functions under extreme conditions. Edge cases in redemption flows, partial redemptions, redemptions during pause, redemptions with stale oracle data, are where bugs hide.
Allowlist and restriction enforcement. Test every transfer restriction path. Attempt transfers to non-allowlisted addresses, from blocklisted addresses, between incompatible jurisdictions. Verify that compliance hooks cannot be bypassed by transferring through an intermediary contract or by using transferFrom with a pre-approved allowance. Confirm that the compliance role has appropriate separation from the mint and upgrade roles.
Oracle safety and fallback behavior. Verify every oracle configuration against its intended price derivation. The February 2026 lending protocol post-mortem revealed a formula error, a token's exchange rate ratio was not multiplied by the base asset's USD price. This is a configuration review, not a code vulnerability, and it requires the auditor to understand the intended price derivation, not just the code's syntax. Check staleness thresholds, deviation bounds, and fallback behavior. Test what happens when the oracle returns zero, returns a negative value, or doesn't respond at all. For a thin-market manipulation attack, evaluate whether the oracle is vulnerable to low-liquidity price manipulation.
Event emission and observability. Every state-changing privileged action must emit an event. Without proper event emission, off-chain monitoring systems are blind to critical changes, and post-incident forensics becomes vastly more difficult. Verify that events contain sufficient data for monitoring tools to detect anomalies, not just that they fire.
Security Requirements Across RWA Asset Classes
Different asset classes carry different risk profiles. Teams tokenizing Treasuries face different primary risks than teams tokenizing private credit or real estate.
Tokenized Treasuries and money market funds: Oracle risk is lower (NAV is relatively stable) but custody risk is paramount. Industry security rankings show that the top-rated protocols in this category achieve their security posture primarily through institutional-grade compliance and custody, not novel smart contract architecture. The primary audit concern is whether the token reliably represents shares in the fund and whether the redemption mechanism works in stressed conditions.
Private credit: Oracle risk is higher because loan pricing is inherently subjective and illiquid. Private credit dominates the tokenized RWA market (approximately 58% of market share according to industry research), with leading platforms structuring senior secured loans, SME financing, and receivables into tokenized formats. The risk of asset–token mismatch is elevated because loan performance data must flow from off-chain servicing systems to on-chain state. Proof-of-reserve attestations for a private credit portfolio are fundamentally harder to verify than for a Treasury portfolio.
Real estate: Legal linkage risk dominates. Property law varies by jurisdiction, and the enforceability of a token holder's claim on an underlying property depends on the SPV structure, the local land registry, and the applicable legal framework. Smart contract risk is typically lower (simpler token logic), but operational risk is higher (property management, tenant relations, and maintenance all happen off-chain with no on-chain visibility).
Resources to Strengthen Your RWA Security Strategy
If you're building, auditing, or investing in an RWA protocol, the time to think about security is while writing your whitepaper, not before launch.
Build your foundation. The QuillAudits RWA Development Handbook gives you the complete mental model: ecosystem landscape, regulatory mapping across jurisdictions, system design patterns, and deep coverage of every major token standard (ERC-4626, ERC-3643, ERC-7540, ERC-1400, and non-EVM equivalents). Whether you're an auditor, protocol engineer, or founder, this is the reference you'll keep coming back to. To complement this foundational knowledge with real-world implementation, teams can partner with Blocsys, a blockchain development and platform engineering company specializing in digital asset infrastructure. From building RWA tokenization platforms and trading systems to designing end-to-end Web3 architectures, Blocsys delivers production-ready solutions tailored for fintech and blockchain ecosystems.
Benchmark your protocol. Use the RWA Security Score Checker, a structured 30+ factor evaluation tool that rates your protocol across 8 critical risk categories with a weighted scoring model. Get a clear picture of where you stand in minutes.
Get a security review. Run a comprehensive audit, covering all five layers of the security stack, before your initial launch and before every major upgrade. The cost of a thorough audit is a fraction of what a single exploit costs in funds lost, trust destroyed, and regulatory scrutiny triggered.
Conclusion
Securing an RWA protocol is not a single audit, it's a continuous practice across four interconnected domains:
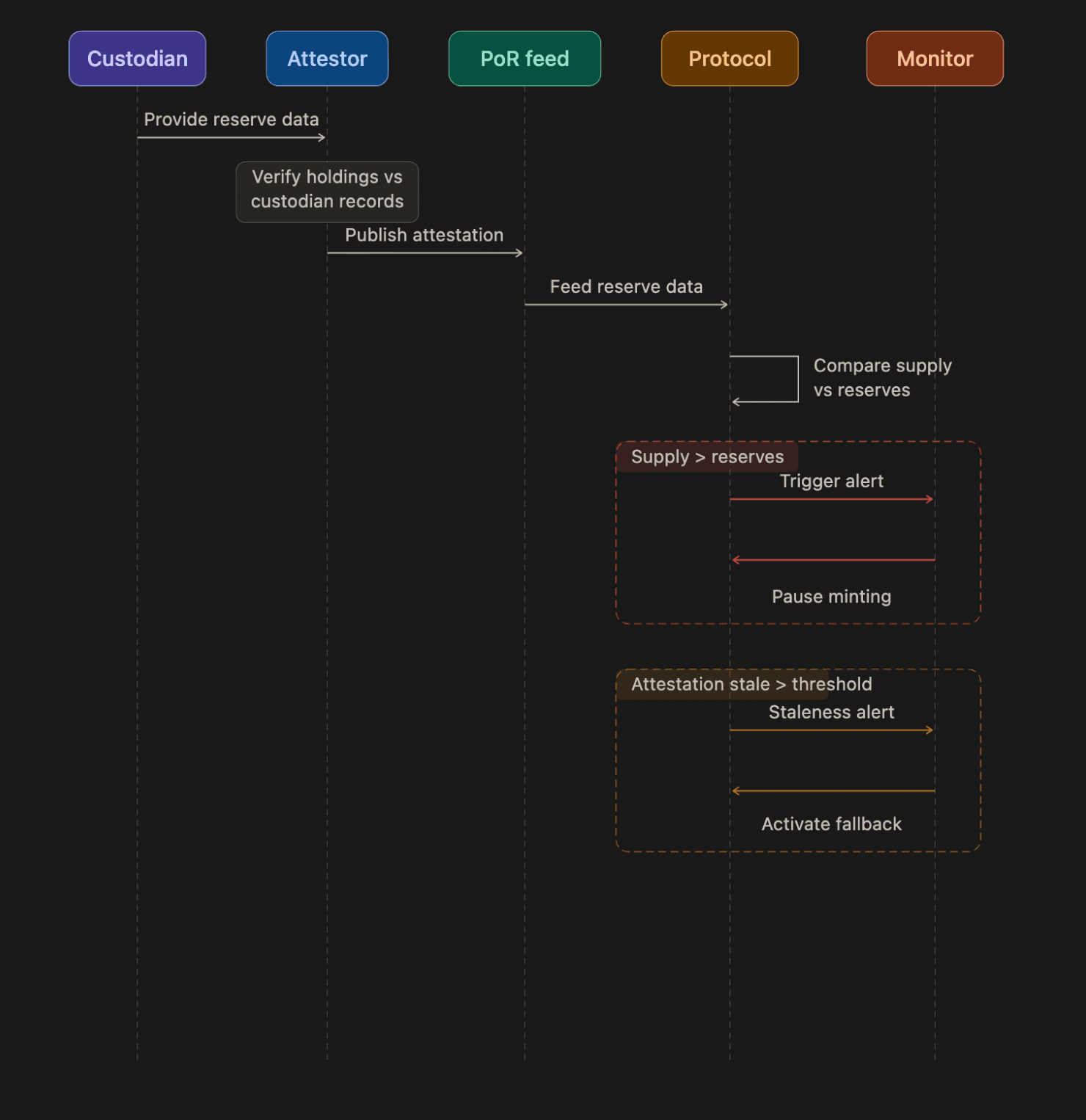
Secure-by-design RWA stack
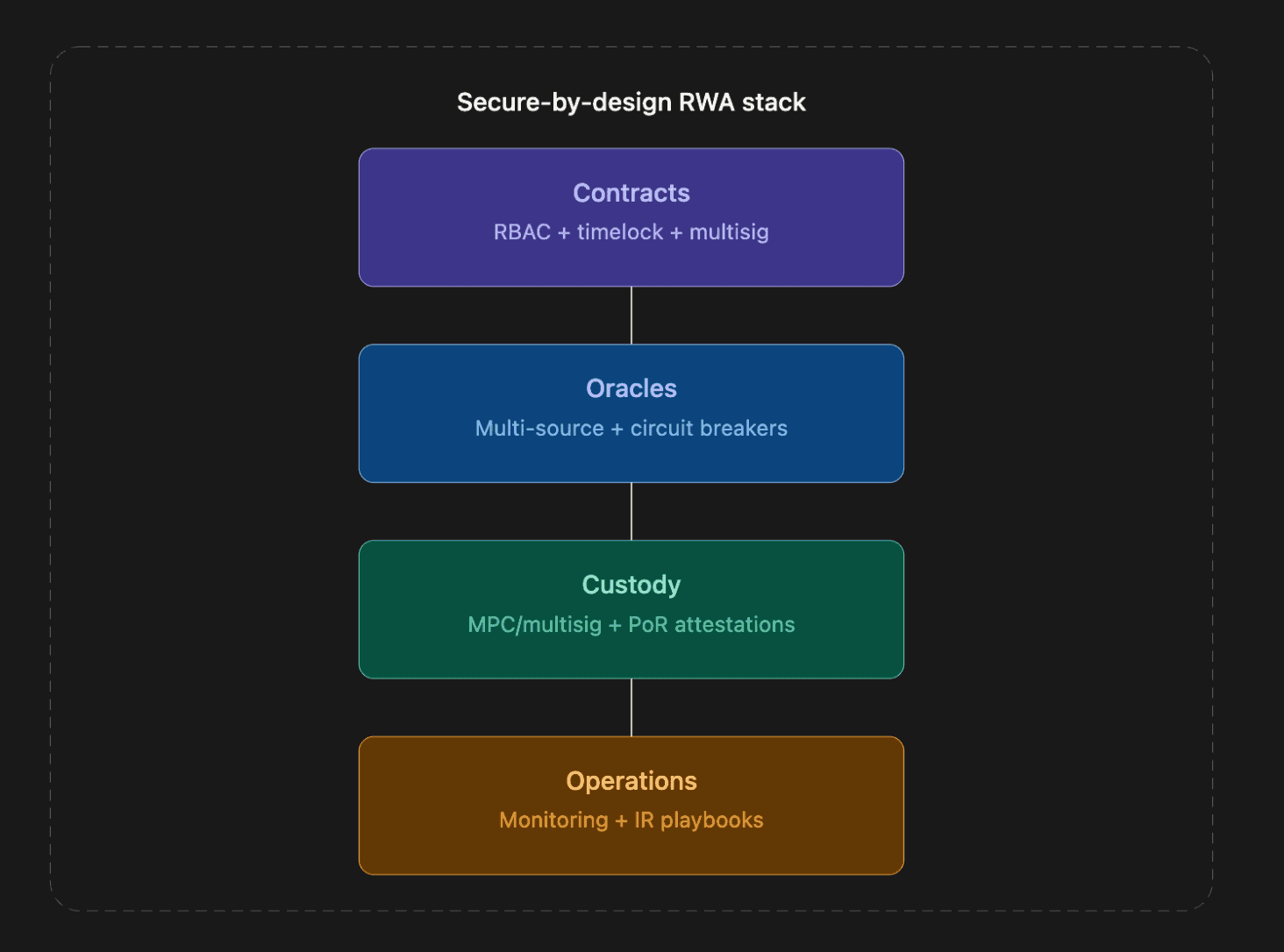
The RWA threat landscape is evolving. The protocols that earn institutional trust and that avoid joining the growing list of RWA exploits will be the ones that treat security as a property of the entire stack, not just the smart contract layer.
Leading consulting firms project a $2 - 4 trillion tokenized asset market by 2030, with some estimates reaching up to $16 trillion. As more value flows on-chain, the incentive for attackers increases proportionally. The winners will be the protocols that build security into their architecture from day one.
Contents




