Resolv Labs $25M Exploit: Unchecked Mint (Explained)
Inside the Resolv Labs $25M exploit, unchecked mint flaw, attack breakdown, impact and how DeFi projects can prevent similar risks.

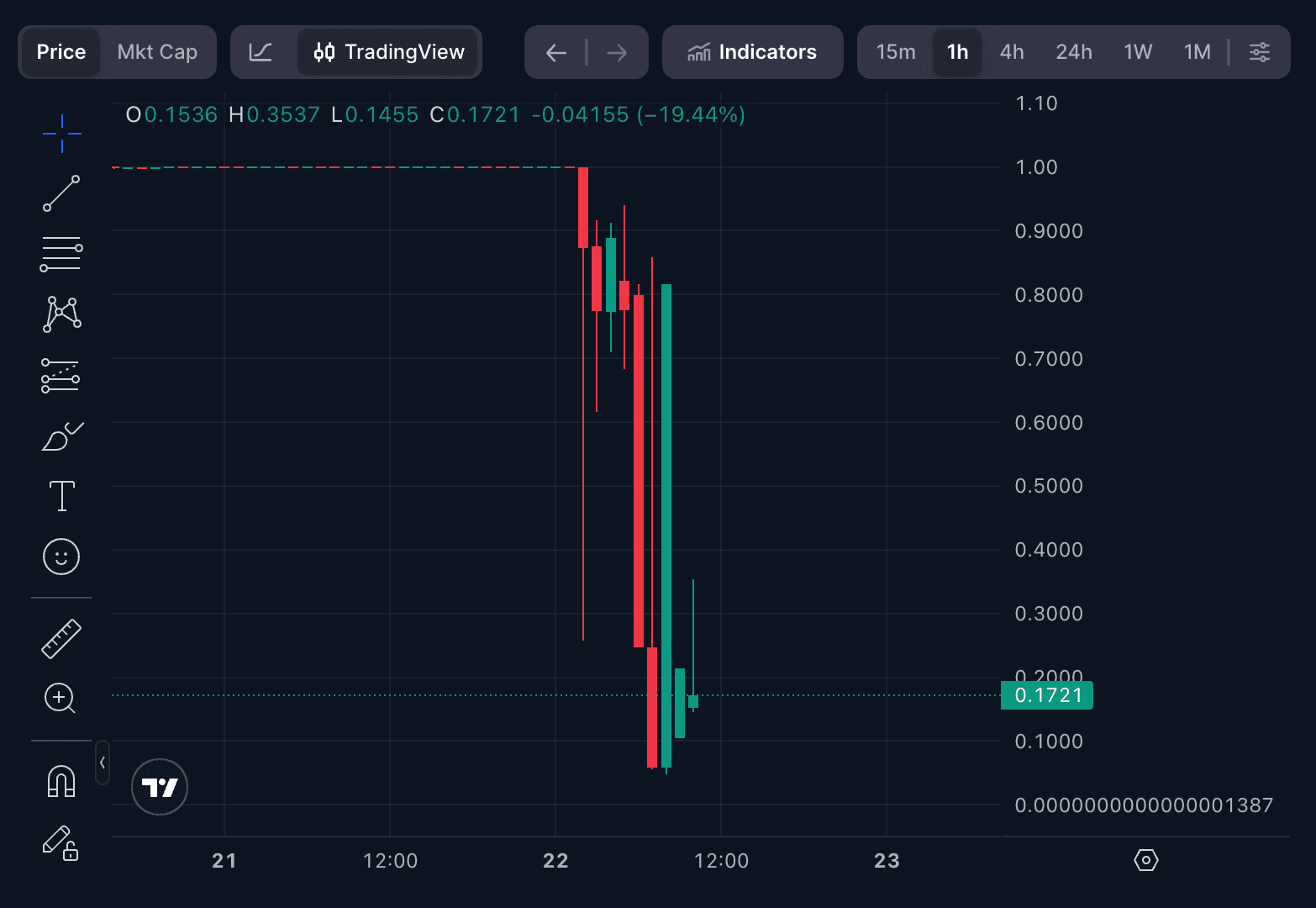
On March 22, 2026, Resolv Labs suffered a critical exploit resulting in approximately $25M in losses. The attacker exploited a fundamental design flaw in the protocol's two-step swap mechanism: while users deposit tokens on-chain, the amount of USR to be minted is passed as an unchecked parameter by an off-chain backend holding SERVICE_ROLE access. Through a compromised EOA or backend, the attacker deposited only $300K USDC across three transactions but minted over 80 million USR tokens. The sudden supply inflation collapsed USR's peg, yet the attacker still extracted $25M, an 83x return on initial capital.
Hack Analysis
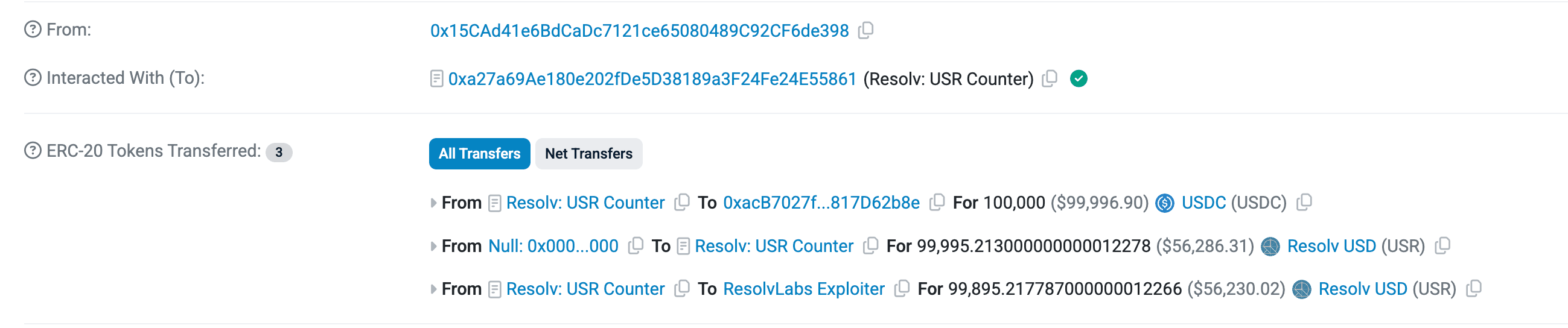
The attacker initiated a swap from USDC to USR tokens, depositing 100K USDC with the intent to receive USR in return.
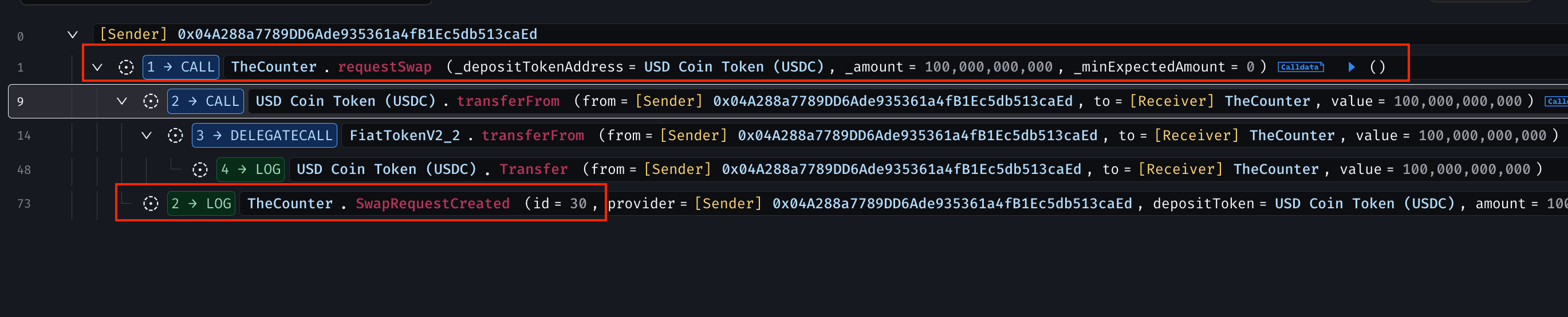
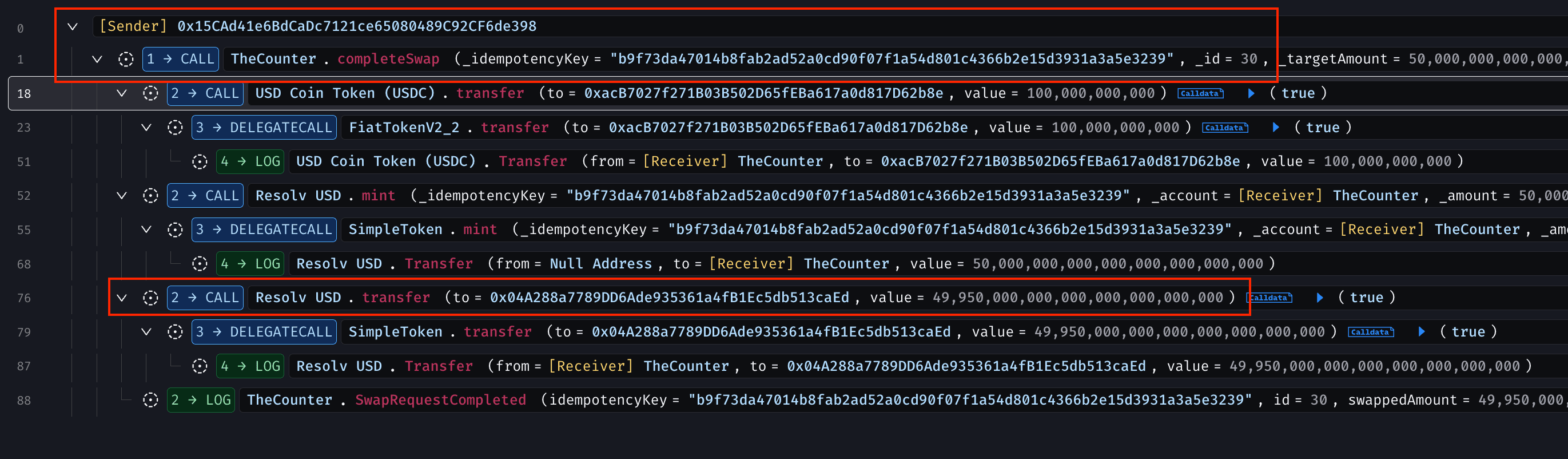
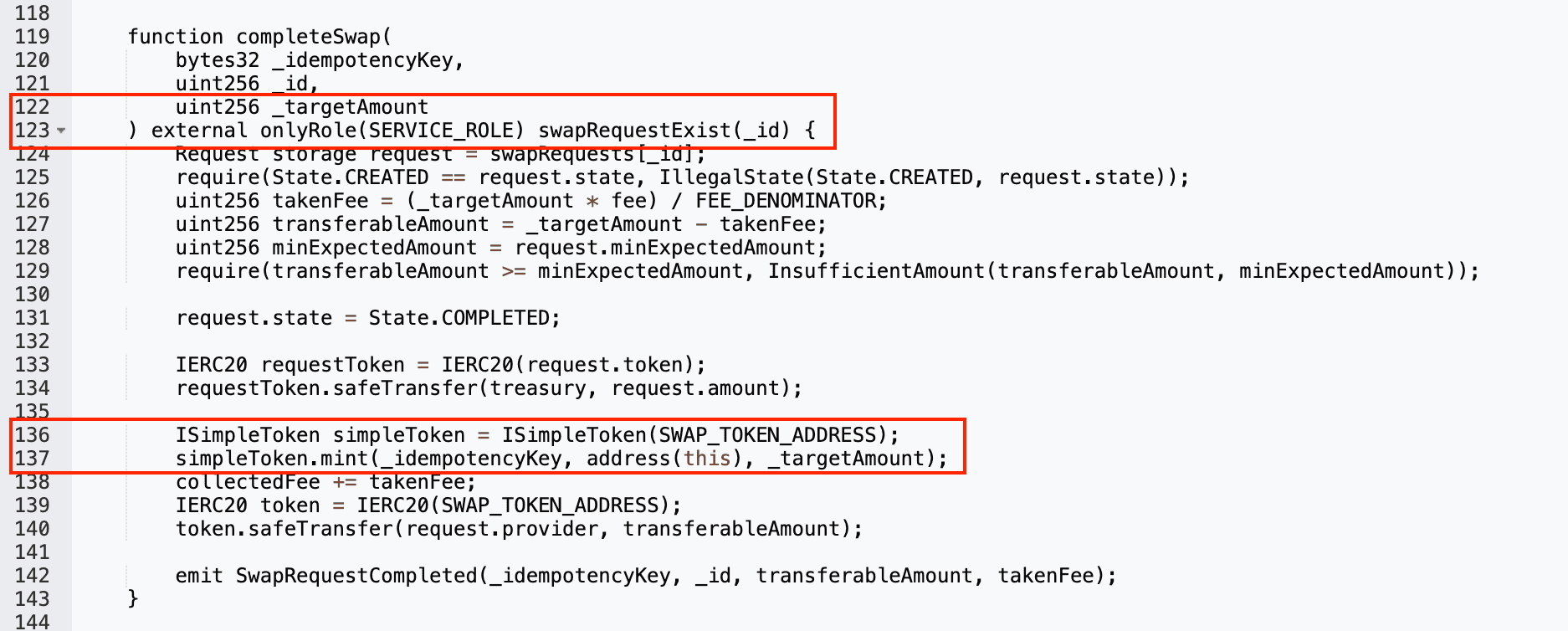
After this, the Resolv Labs backend calls completeSwap()after performing its checks off-chain. However, the amount of USR to be minted is passed directly as a parameter.
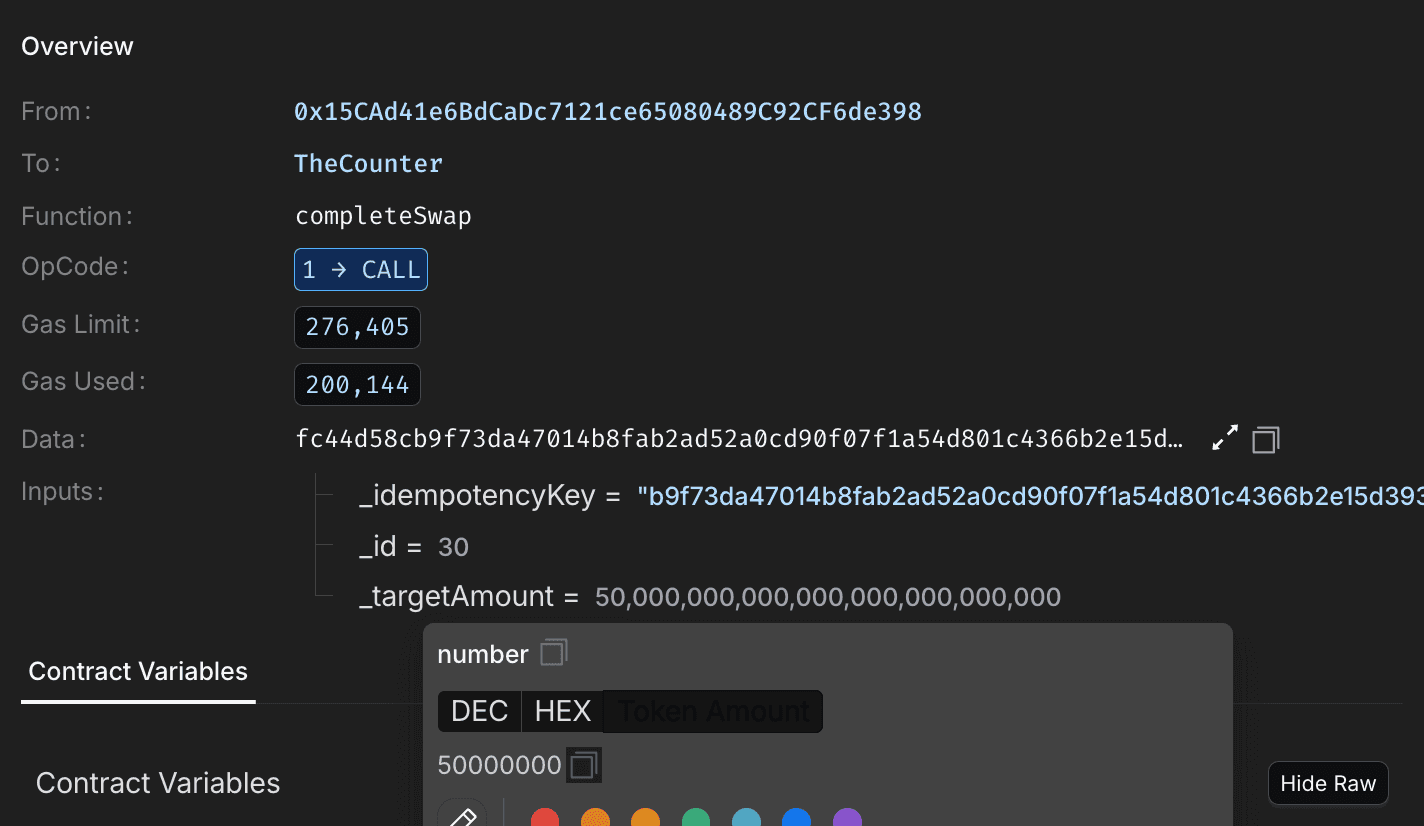
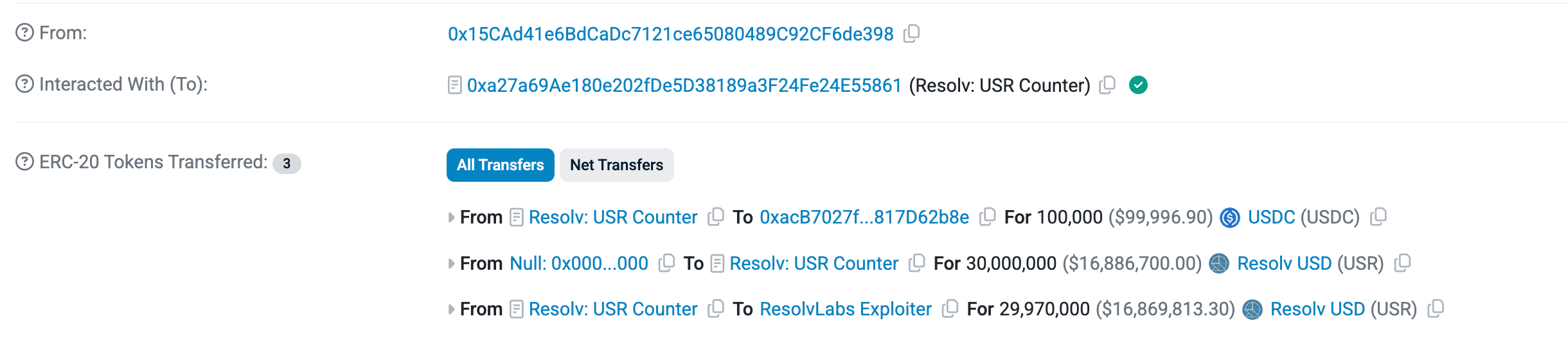
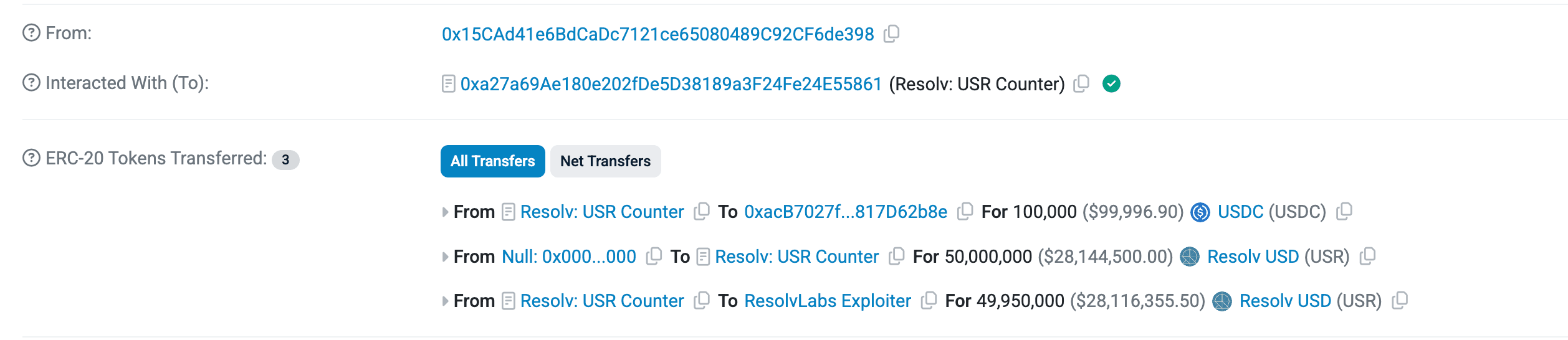
The attacker initially submitted a requestSwap with 100K USDC, but the Resolv Labs backend passed a mint amount of 50M USR, far exceeding what would be expected for a stablecoin swap of that size. After deducting protocol fees, the attacker received 49.95M USR.
The attacker repeated this process three times, minting a total of 80M USR tokens by providing only 300K USDC. Although these tokens were initially worth $80M as a stablecoin, the peg collapsed due to the artificially inflated supply. Even so, the attacker managed to extract around $25M, achieving roughly an 83x return on the initial capital.

The diagram below illustrates the full attack flow, from the initial swap request to the final fund extraction.

Root Cause
The protocol uses a two-step process to mint USR tokens. First, a user calls requestSwap() and provides a whitelisted token. Then, the backend calls completeSwap(), which is restricted to an address with the SERVICE_ROLE, and specifies the amount of USR to be minted after deducting protocol fees.
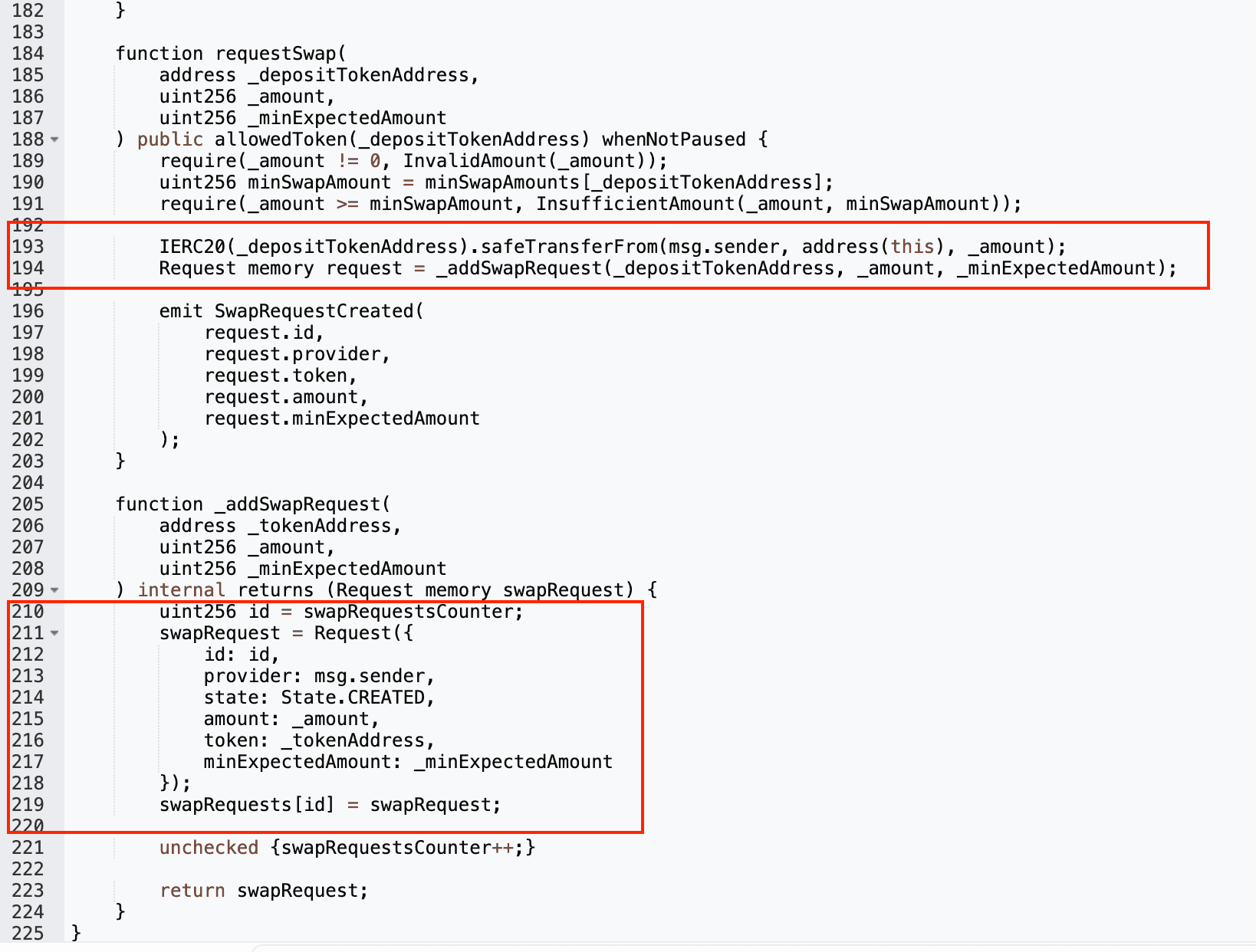
The issue arises because the mint amount is fully determined by the caller, with no on-chain validation to ensure it is proportional to the deposited token value. As a result, targated infrastructure compromise and cyberattack (0x15cad41e6bdcadc7121ce65080489c92cf6de398), the attacker deposited around $100K per transaction but minted significantly more USR than they should have.
How QuillAudits On-Chain Monitoring Could Have Prevented This
This exploit unfolded across three transactions over a short window. At no point did an on-chain safeguard flag the 500x deviation between deposited value and minted tokens. With real-time on-chain monitoring in place, the attack could have been detected and contained after the very first transaction.
Here's exactly where QuillAudits On-Chain Monitoring would have intervened:
Detection Point #1 Mint-to-Deposit Ratio Breach
The core invariant for any stablecoin minting flow is simple: minted value ≈ deposited value. The attacker deposited 100K USDC but triggered a mint of 50M USR a 500x deviation. QuillAudits Protocol-Aware Custom Guards model exactly these business-logic invariants. A guard configured as mintedAmount <= depositedAmount * maxSlippage would have fired instantly on Transaction #1.
Detection Point #2 Abnormal Supply Inflation
80M USR minted in minutes against a total circulating supply represents an extreme supply spike. QuillAudits Economic & Oracle Risk Surveillance continuously tracks supply changes, TVL shifts, and peg stability for stablecoin protocols. A sudden multi-million token supply surge would have triggered a critical economic anomaly alert.
Detection Point #3 Privileged Role Behavior Anomaly
The SERVICE_ROLE address executed three high-value completeSwap() calls in rapid succession, each minting orders of magnitude more than the corresponding deposit. QuillAudits Real-Time Transaction Monitoring tracks every privileged-role interaction per block flagging unusual frequency, abnormal parameters, or deviation from historical patterns.
What Could Have Happened With Monitoring?
| Stage | Without Monitoring (What Happened) | With QuillAudits Monitoring (What Could Have Happened) |
|---|---|---|
| Transaction #1 | 100K USDC → 50M USR minted. No alert. | Invariant guard fires. Slack/PagerDuty alert sent to team in seconds. |
| Between Tx #1 and #2 | No detection. Attacker proceeds freely. | Team receives critical alert. Auto-pause on completeSwap() triggered via automated response pipeline. |
| Transactions #2 & #3 | Attacker mints another 30M USR. | Blocked. Protocol paused. Damage limited to ~$8M (Tx #1 only). |
| Post-exploit extraction | Attacker swaps 80M USR → wstUSR → ETH. $25M extracted. | With early pause, attacker holds USR that can be frozen or the swap path is blocked. Extraction prevented. |
| Total Loss | ~$25M | Could have been limited to ~$8M or less |
The Takeaway
An audit secures code at a point in time. But when a privileged backend key is compromised as happened here only continuous runtime monitoring can catch the exploit as it unfolds. The gap between audited and monitored is where $25M was lost.
QuillAudits On-Chain Monitoring delivers real-time protocol visibility, invariant-level threat detection, and automated incident response — turning a one-time audit into continuous, always-on defense.
Funds Flow After Attack
The attacker converted all USR tokens into wstUSR through a simple deposit call.
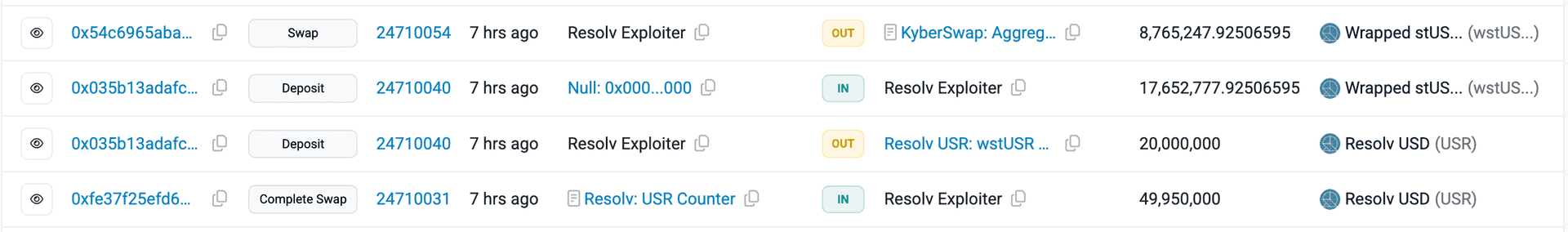
Then, through multiple swaps, the attacker converted them into USDC and USDT, and eventually into ETH.
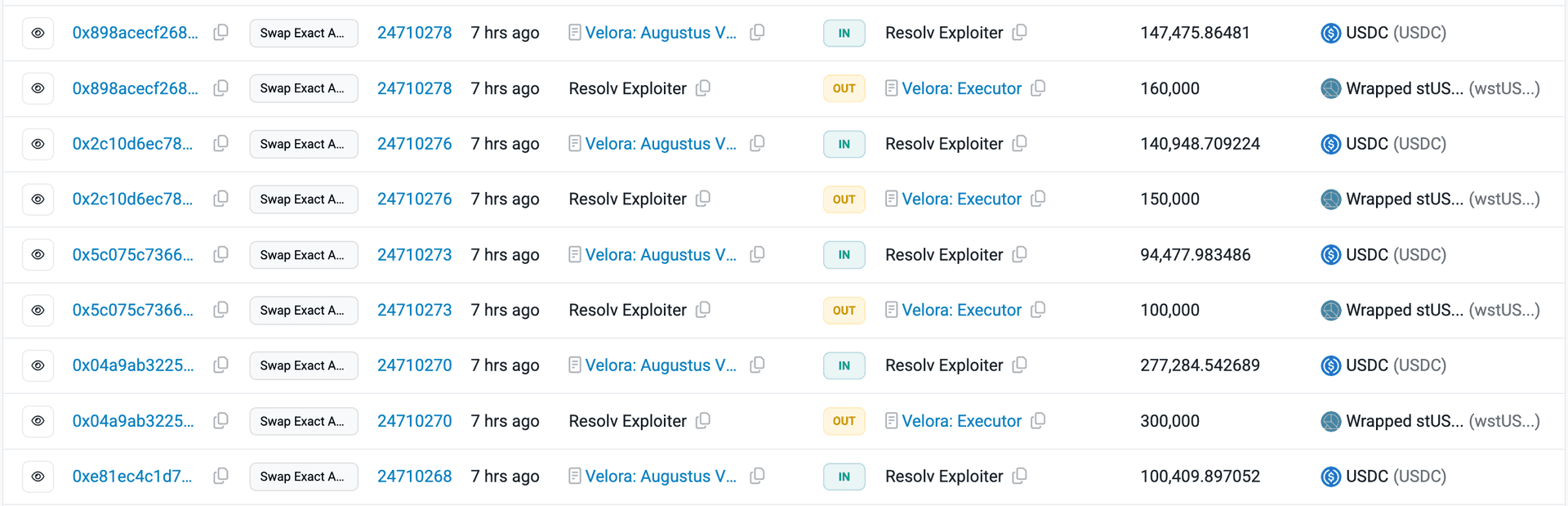
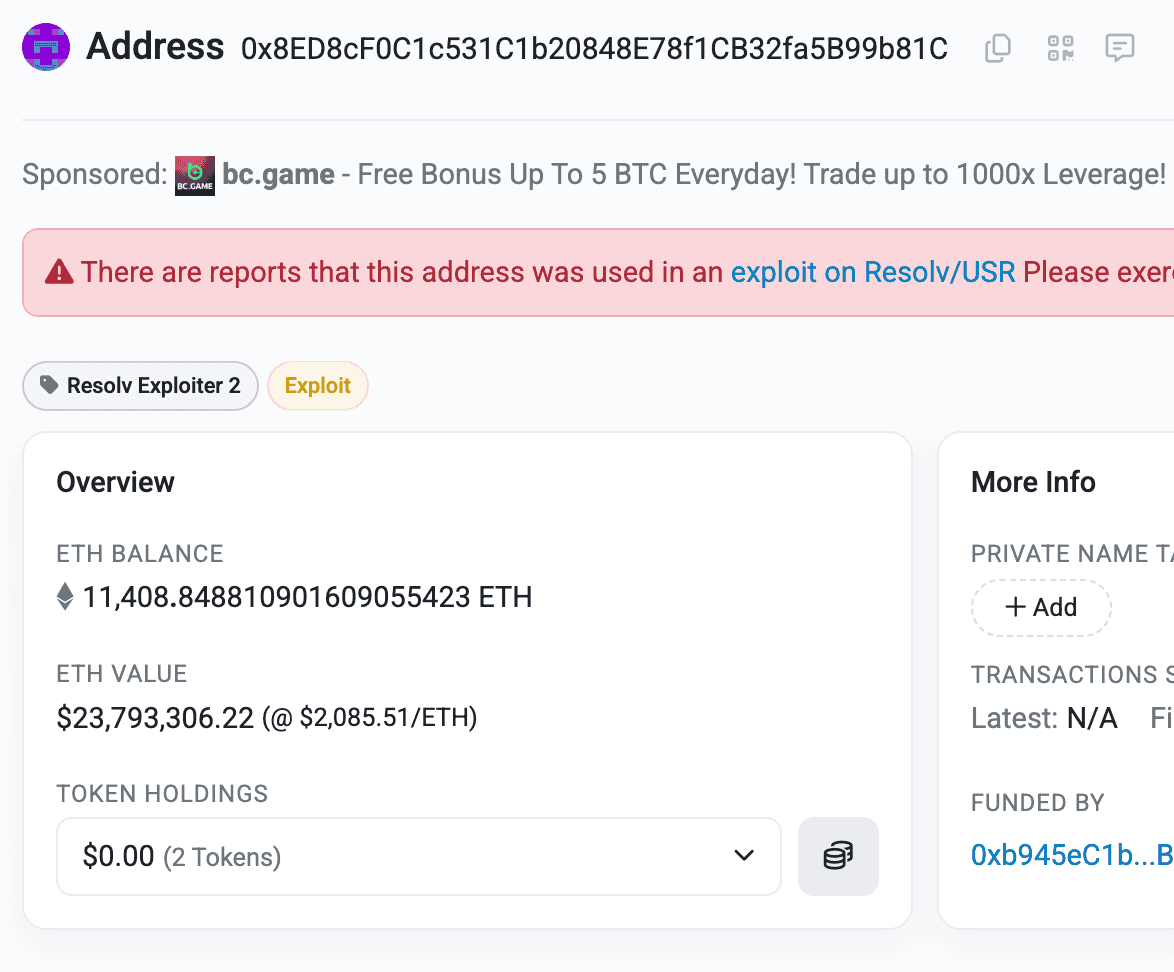
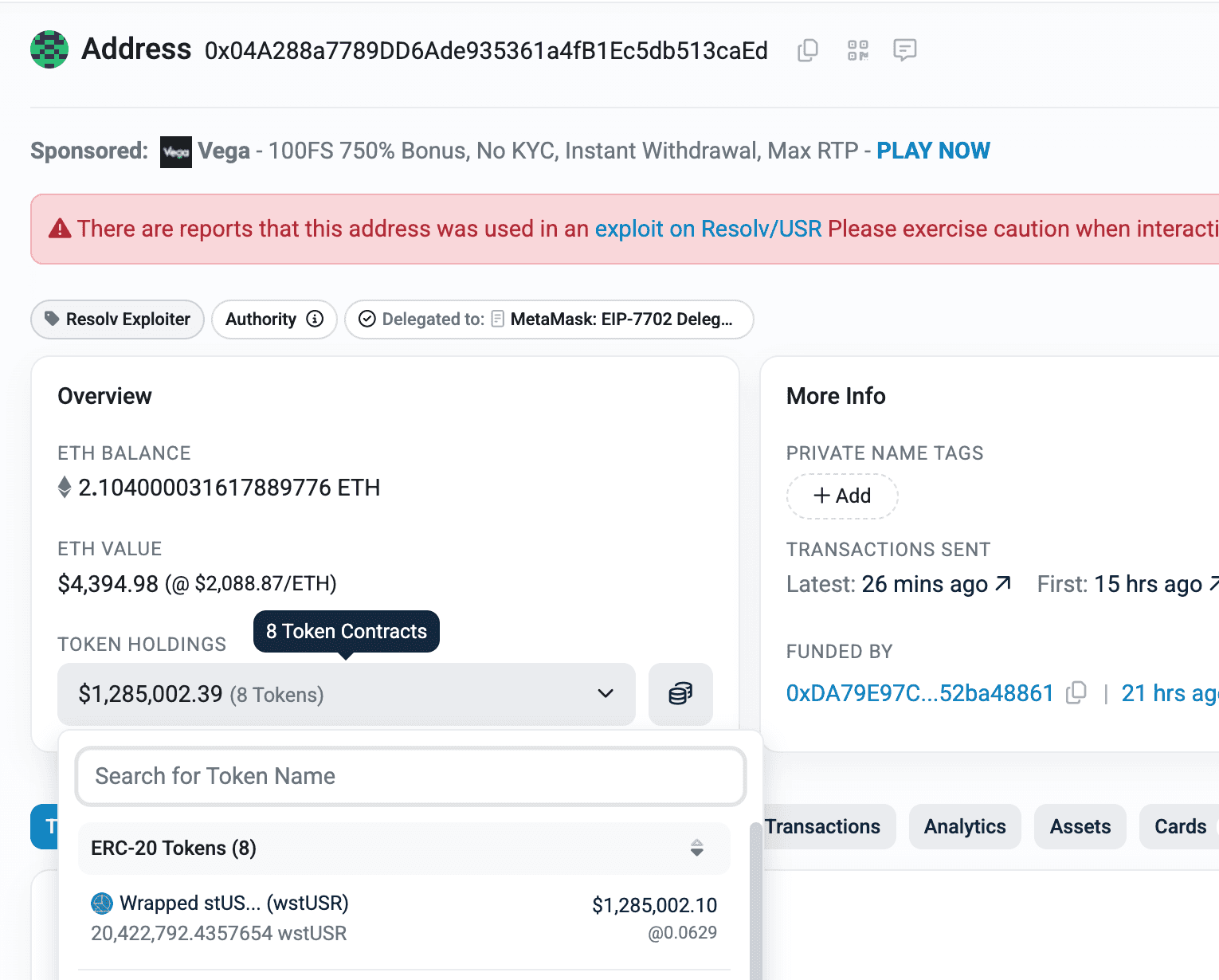
At the time of writing, the attacker has extracted $23.7M worth of ETH and $1.2M worth of wstUSR, all of which are currently held in the attacker’s EOA.
The attacker minted over 80M USD tokens (a stablecoin) from thin air. As the peg collapsed due to the sudden supply increase, the token’s value dropped, but the attacker still managed to extract around $25M by putting in just $300K USDC.
Post Attack Mitigation
The Resolv Labs team has acknowledged the attack and paused all protocol operations.
Team confirmed the exploit resulted from a targeted infrastructure compromise and cyberattack by an unauthorized third party, and outlined recovery steps.
Team confirmed the exploit resulted from a targeted infrastructure compromise and cyberattack by an unauthorized third party, and outlined recovery steps.
On April 4, 2026, Resolv published a post-mortem revealing a March 22 multi-stage attack on its off-chain infrastructure, resulting in 80M USR illicitly minted and $25M extracted as ETH.
Relevant Address and Transactions
Attacker EOAs
- 0x04a288a7789dd6ade935361a4fb1ec5db513caed
- 0x8ED8cF0C1c531C1b20848E78f1CB32fa5B99b81C
- 0xb945ec1be1f42777f3aa7d683562800b4cdd3890
Compromised SERVICE_ROLE EOA
Attack transactions
- 0x41b6b9376d174165cbd54ba576c8f6675ff966f17609a7b80d27d8652db1f18f
- 0x7f914328a67f7094eedb0efda7aef74aafdb7f862ad7bc78259564fd453a931d
- 0xfe37f25efd67d0a4da4afe48509b258df48757b97810b28ce4c649658dc33743
Request swap transactions
- 0x590b5c66df27b7f34cde721ca1b5f973ae047ffda370610491f694dade732c89
- 0x2989be8683cdc9eec0e1e877d826624140405982bb63decdf4504b75b55a6757
- 0xe5bae64ee813c742f06b5d045397c2eefa31532e4d6c21b7c6da129eaa17ae4b
Resolv USR Contract
Resolv wstUSD Token Contract
Conclusion
The Resolv Labs hack highlights the systemic risk of delegating critical financial logic to off-chain actors without on-chain safeguards. Mint amounts must be validated on-chain relative to deposited value, no off-chain role should have unchecked minting authority. Protocols using privileged backend keys should enforce threshold signatures (e.g. MPC-based TSS wallets) for any automated signing, ensuring no single compromised key can trigger catastrophic state changes. Defense-in-depth, combining on-chain invariants with multi-party key management, is non-negotiable for protocols handling user funds at scale.
Contents




