YeildBlox $10M Hack (Oracle Manipulation - Explained)
Oracle manipulation led to a $10M YieldBlox hack. Explore the attack mechanics, vulnerabilities and lessons for stronger DeFi defenses.

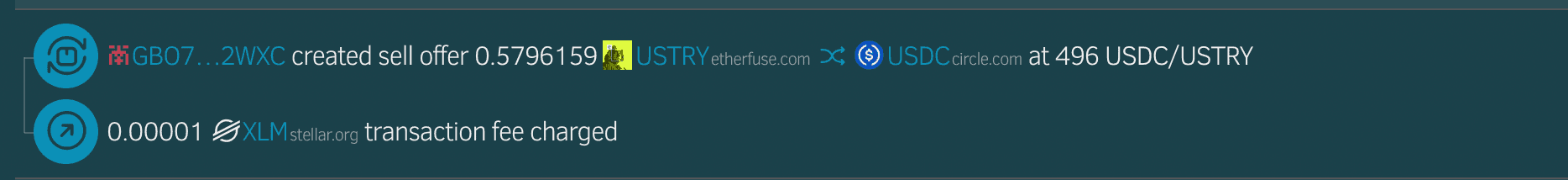
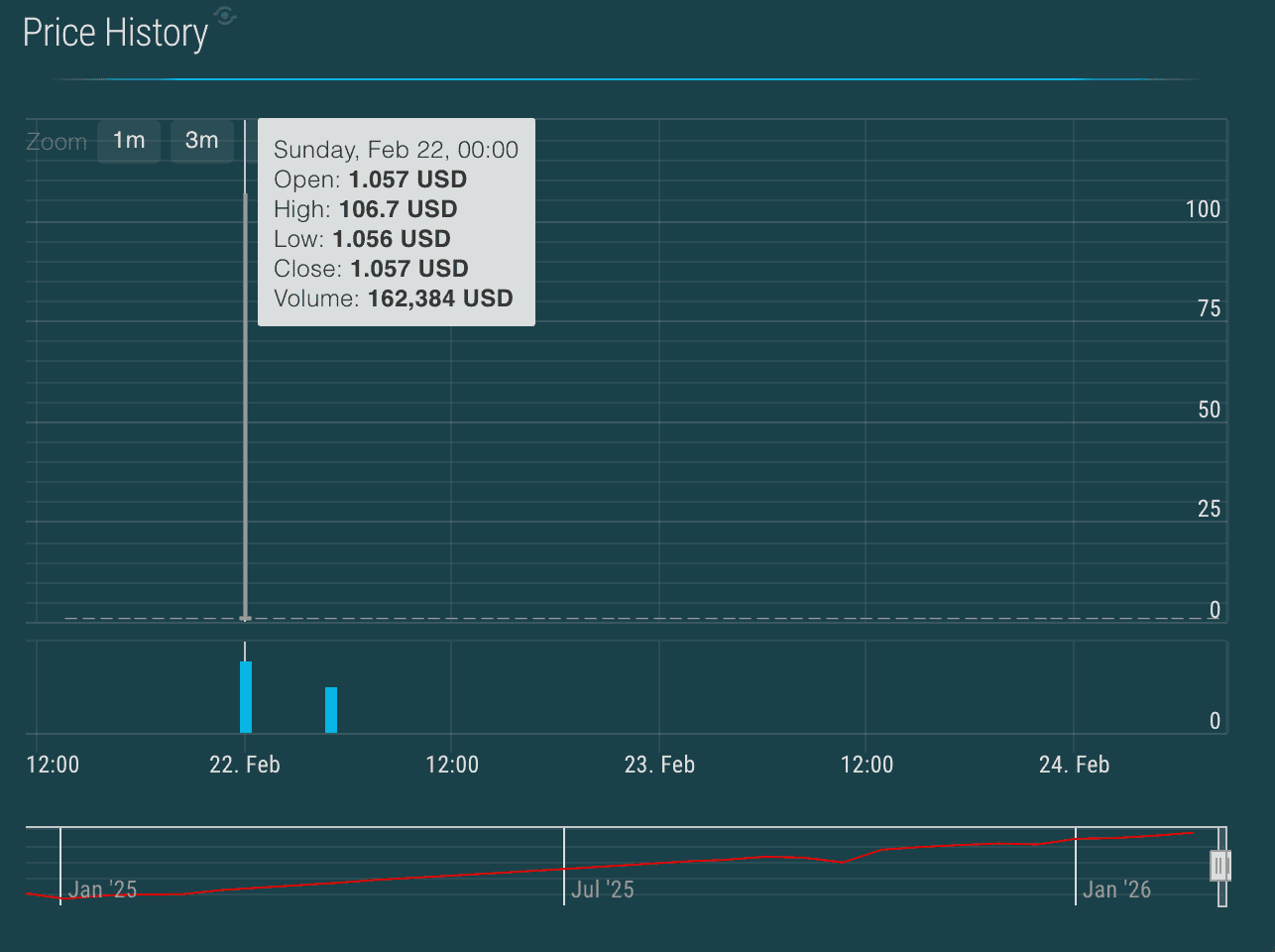
On February 22, 2026, the community managed YieldBlox Blend pool on Stellar was exploited through a classic thin-liquidity oracle manipulation attack, resulting in more than $10M in losses. The attacker targeted the illiquid USTRY/USDC market on the Stellar DEX, where trading volume was negligible and market depth was effectively nonexistent. By executing a single abnormal trade, the USTRY price was inflated over 100× within the oracle’s VWAP window.
Because the protocol relied on this oracle price without additional liquidity or sanity safeguards, the manipulated valuation was treated as legitimate collateral value. The attacker then supplied USTRY and borrowed significant amounts of USDC and XLM, creating substantial bad debt in the pool. This report breaks down the attack mechanics, root cause, fund flows, and post-incident mitigation efforts.
Hack Analysis
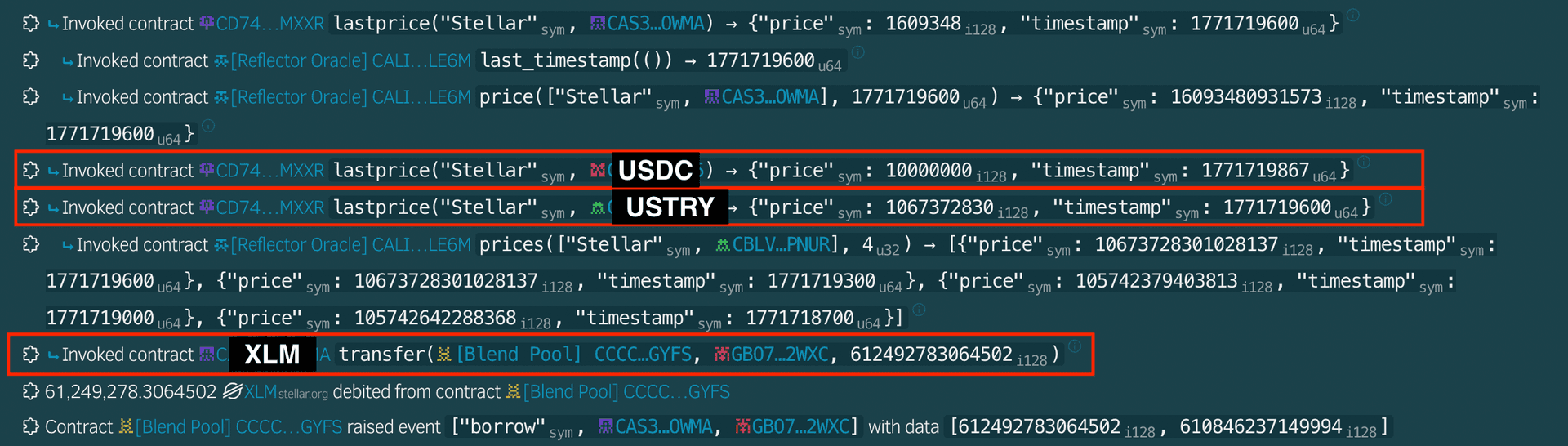
The attacker manipulated the USTRY price on the Stellar DEX by exploiting the extremely illiquid USTRY/USDC market. A single abnormal trade inflated the asset price from approximately ~$1 to ~$106. With no additional trades occurring within the VWAP window, the oracle updated and reported the inflated price.
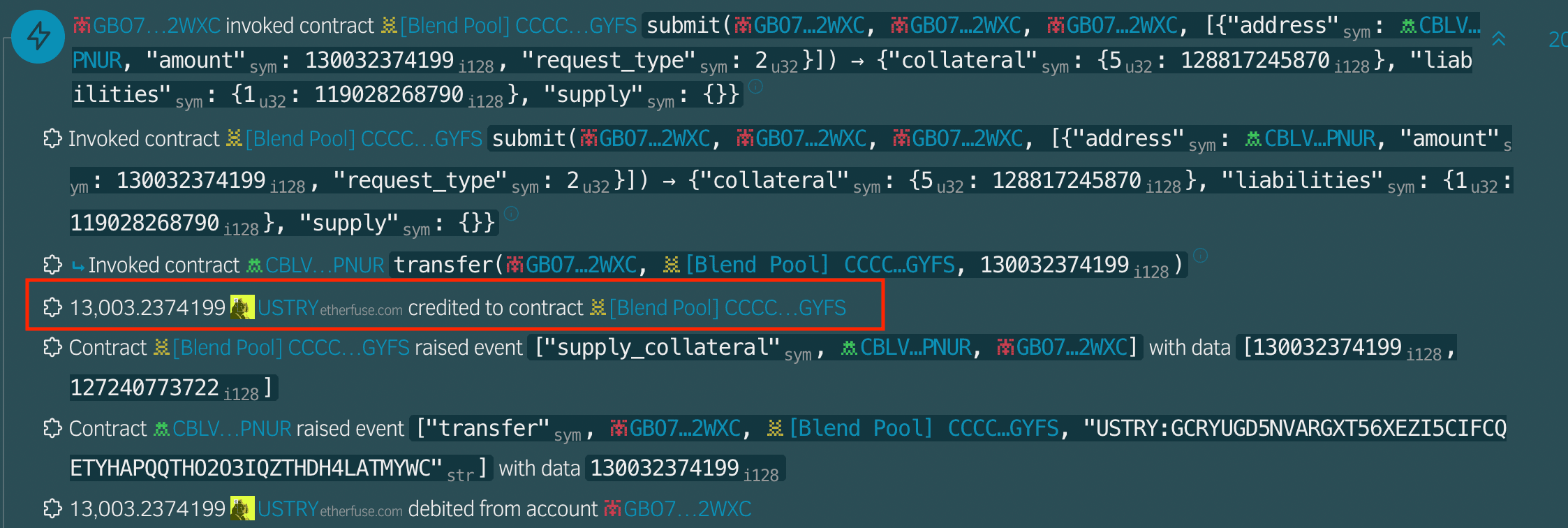
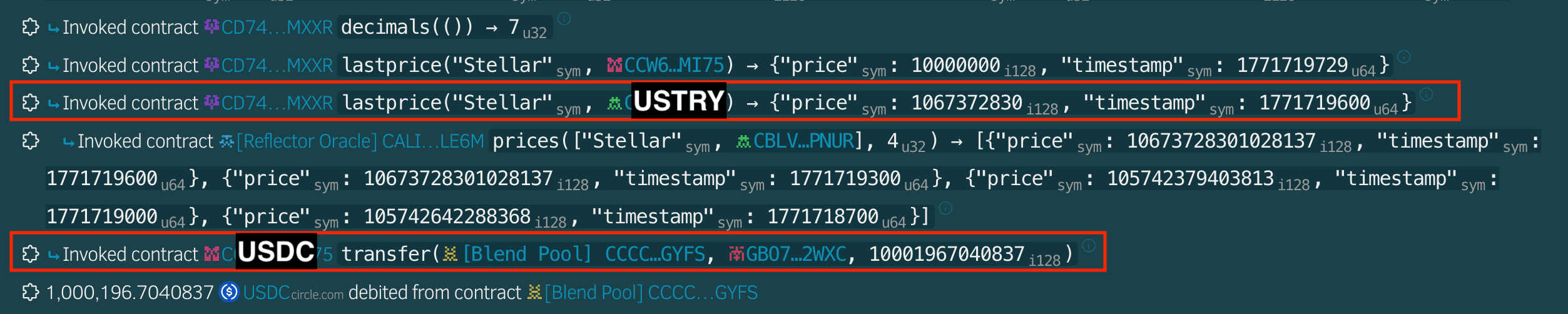
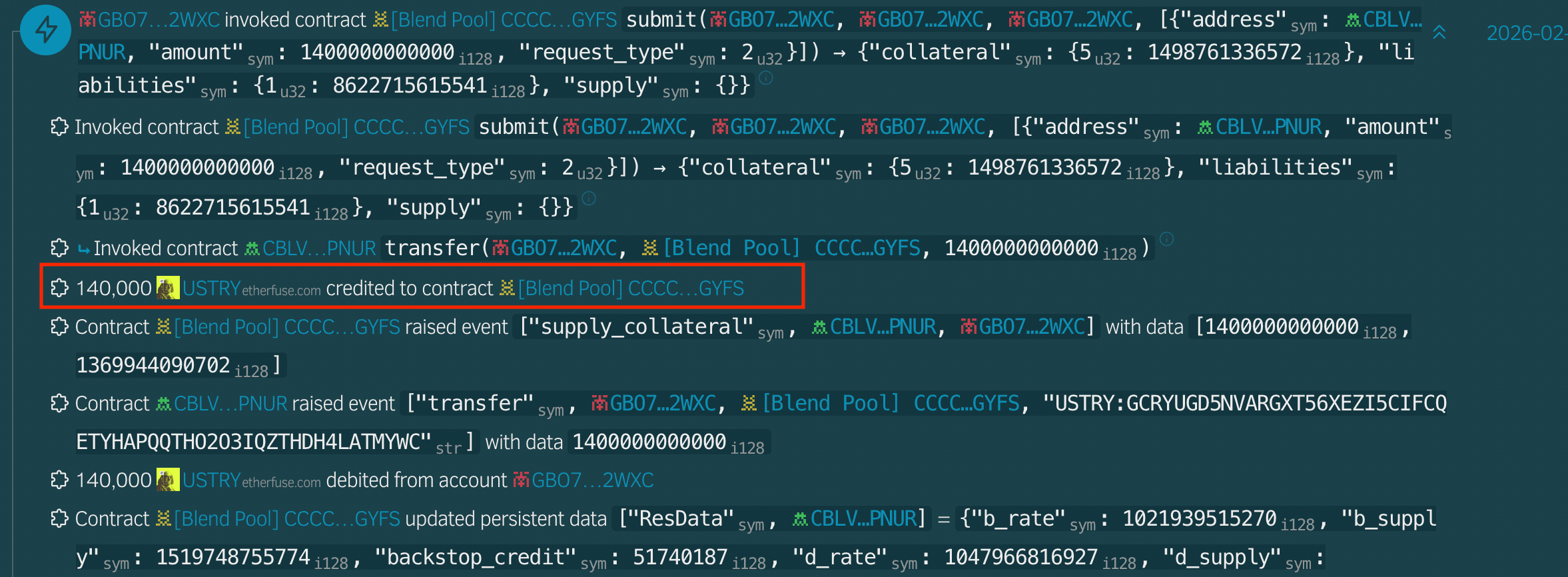
The attacker first supplied 13,003 USTRY as collateral into the affected YieldBlox (Blend V2) pool. Due to the manipulated oracle price, the protocol significantly overvalued this collateral, enabling the attacker to borrow 1,000,196.70 USDC.
The attacker then supplied an additional 140,000 USTRY as collateral. Leveraging the inflated valuation, the attacker borrowed 61,249,278.31 XLM, further extracting value from the pool.
The diagram below summarizes the exploit flow, from oracle price manipulation in an illiquid market to overcollateralized borrowing and eventual bad debt creation in the pool.

Root Cause
YieldBlox relied on Reflector as its price oracle, which sources USTRY pricing from the Stellar DEX (SDEX) using a VWAP-based aggregation model. However, the USTRY/USDC market on SDEX had extremely low liquidity, with less than $1 in hourly trading volume and no meaningful market depth.
The attacker executed a single trade that inflated the USTRY price from approximately $1 to $106 (over a 100× increase). Critically, there were no additional trades for more than 10 minutes following this manipulation. Due to the absence of trading activity during the VWAP window, the manipulated trade dominated the time-weighted average calculation, causing the oracle-reported price to shift from ~$1 to ~$106.
Because the protocol trusted this VWAP derived price without additional liquidity or sanity checks, it treated the inflated valuation as legitimate. The attacker then deposited USTRY as collateral and borrowed substantial amounts of XLM and USDC against the artificially inflated price, leading to the exploit.
Protect Your Protocol from Oracle Manipulation
Protect Your Protocol from Oracle Manipulation
Thin liquidity and unchecked VWAP models can turn a single trade into a $10M exploit. We audit oracle integrations, liquidity assumptions and economic attack surfaces before attackers do.
Funds Flow After Attack
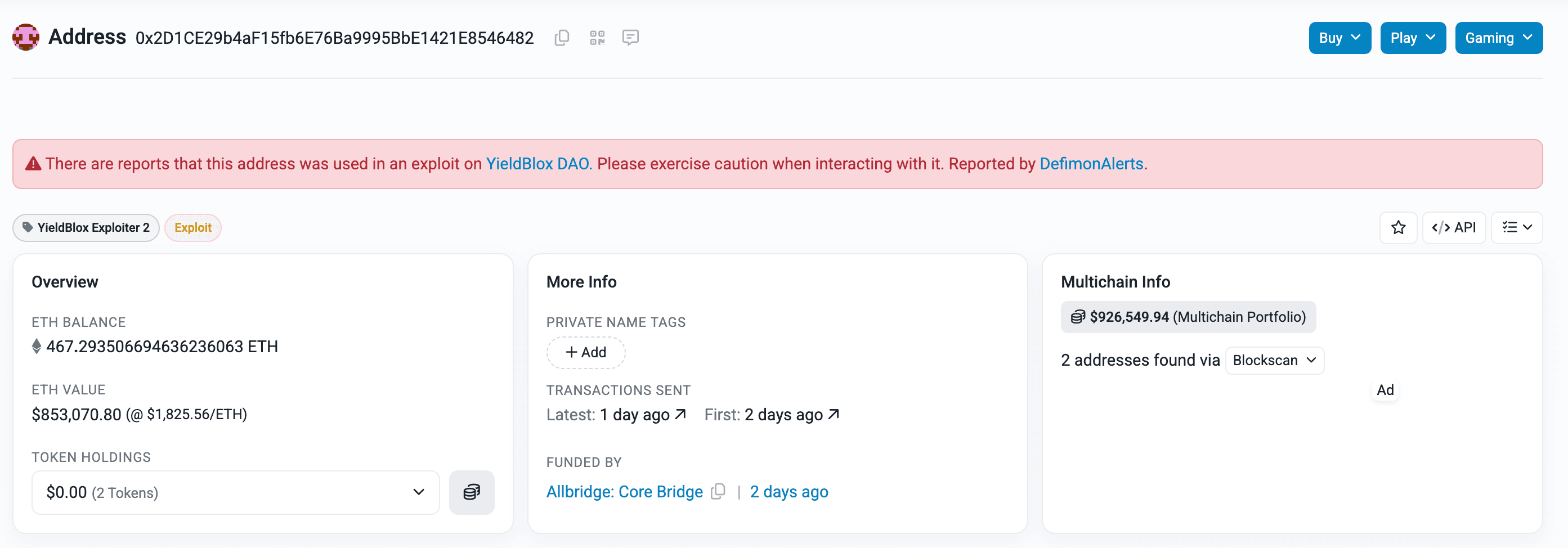
The attacker swapped the stolen tokens into USDC and then bridged the funds from Stellar to Base using Allbridge, before moving them further from Base to Ethereum via Across and Relay.

On Ethereum, Base, and BNB Chain, the bridged funds are still sitting in the attacker’s wallet (0x2D1CE29b4aF15fb6E76Ba9995BbE1421E8546482), with no significant outflows observed at the time of writing.
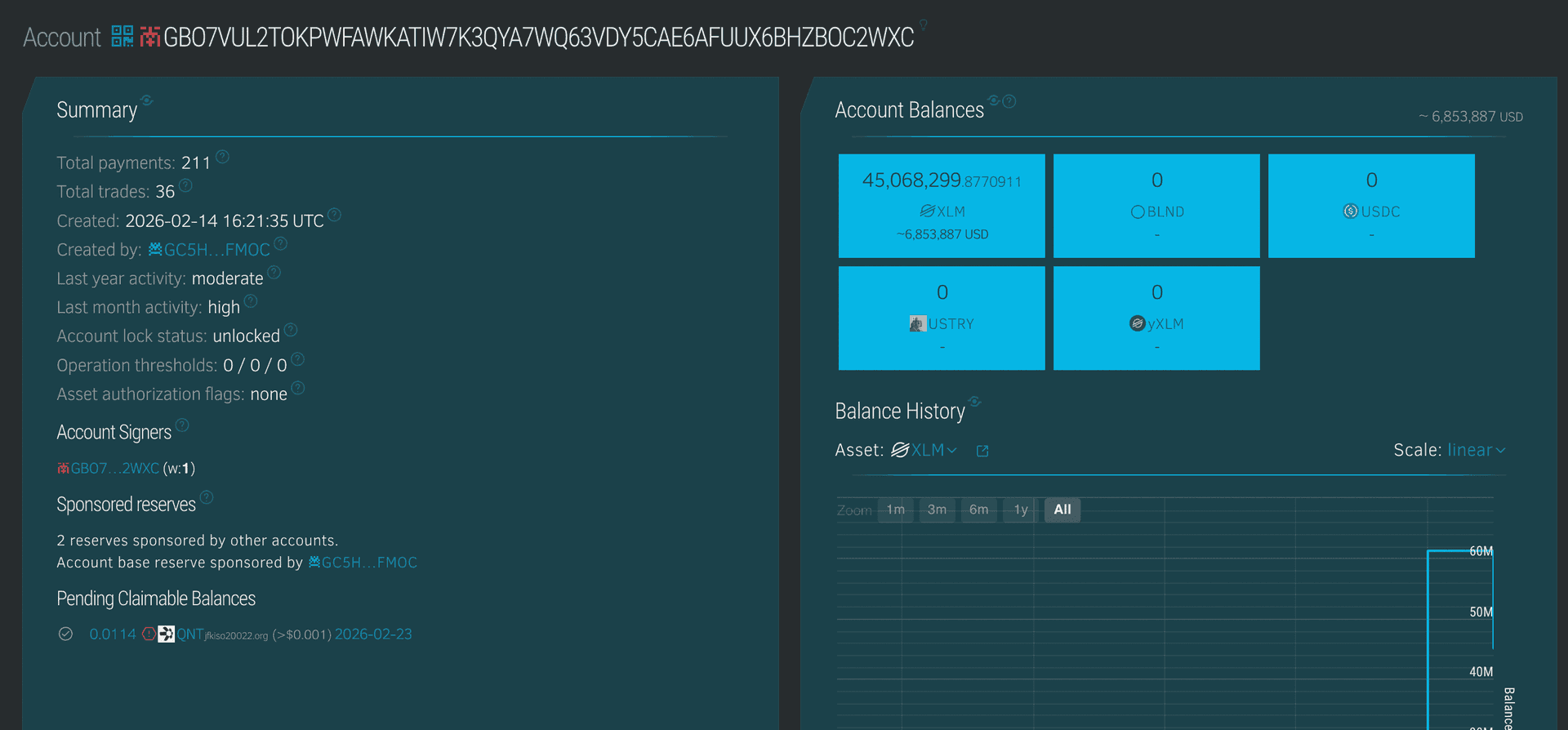
Roughly $6.7 million worth of XLM is still sitting in the attacker’s Stellar wallet, and the funds are gradually being sent to multiple addresses, likely in an effort to spread them out and make tracking more difficult.
Post Attack Mitigation
Reflector confirmed that its infrastructure was not exploited, it reported prices derived from the Stellar DEX using a VWAP-based model. The manipulation was made possible due to extreme illiquidity in the USTRY/USDC market, where a single trade inflated the price ~100× and no additional trades occurred within the window. Reflector stated that other assets with meaningful liquidity and multiple active traders are not at risk.
Script3 is coordinating remediation efforts and confirmed that all EURC, USDC, and XLM depositors in the affected YieldBlox Lending Pool will be fully compensated for losses caused by bad debt. The incident was isolated to a single community-managed pool, and no other Blend pools were affected or vulnerable. A significant portion of the stolen funds has been frozen.
Relevant Address and Transactions
Attacker Wallet: GBO7VUL2TOKPWFAWKATIW7K3QYA7WQ63VDY5CAE6AFUUX6BHZBOC2WXC
Attacker EVM Wallet:
0x2D1CE29b4aF15fb6E76Ba9995BbE1421E8546482
XLM Borrow Transaction:
3e81a3f7b6e17cc22d0a1f33e9dcf90e5664b125b9e61f108b8d2f082f2d4657
USDC Borrow Transaction:
ae721cacee382bdecac8d2c47286ecd42cb4711f658bb2aec7cba60dc64a31ff
USTRY:
CBLV4ATSIWU67CFSQU2NVRKINQIKUZ2ODSZBUJTJ43VJVRSBTZYOPNUR
USTRY Supply Transactions:
- b810ba4a8d7547bb024f17b58c32cc644533176206d0f8178d4ba0a545cb7597
- 81f304ae627ba294df0f9c0708a58a2fe770b39d65f8cd0efe1d7d6d6cc885a6
Conclusion
The YieldBlox exploit was not caused by a smart contract vulnerability, but by an economic design weakness rooted in oracle dependency on an illiquid market. A single manipulated trade in a near-zero volume orderbook was enough to distort the VWAP-based price feed, enabling the attacker to significantly overvalue collateral and extract millions in assets. This incident highlights the critical importance of liquidity thresholds, market depth validation, and circuit breakers when relying on on-chain DEX pricing. Even mathematically sound oracle systems can fail if underlying market conditions are economically unsound. Robust oracle design must account not just for price accuracy, but for market quality and resilience.
Contents




